1、什么是CSRF?
已经有很多博文讲解其过程和攻击手段,在此就不重复了。 O(∩_∩)O 不清楚的同学,请自行搜索或按链接去了解: http://blog.csdn.net/Flaght/article/details/3873590
2、CSRFGuard_Project
开源项目 CSRFGuard,介绍了如何使用在 HTTP 请求中加入 token 并验证的方法来抵御 CSRF。 https://www.owasp.org/index.php/Category:OWASP_CSRFGuard_Project
3、检测CSRF方法?
OWASP上面有一个叫做CSRFTester的工具,可以构建进行测试。
下载链接:https://www.owasp.org/index.php/CSRFTester
教程指引:http://www.zyiqibook.com/article216.html
4、如何防御CSRF?
我们采用CSRFGuard_Project方案 JAVA DOM方式。
配置如下:
1)引入csrfguard-3.1.0.jar到你的工程: 2)配置web.xml:
<!-- 基于复杂方案OWASP CsrfGuard的CSRF安全过滤 -->
<servlet>
<servlet-name>JavaScriptServlet</servlet-name>
<servlet-class>org.owasp.csrfguard.servlet.JavaScriptServlet</servlet-class>
</servlet>
<servlet-mapping>
<servlet-name>JavaScriptServlet</servlet-name>
<url-pattern>/JavaScriptServlet</url-pattern>
</servlet-mapping>
<context-param>
<param-name>Owasp.CsrfGuard.Config</param-name>
<param-value>WEB-INF/csrfguard.properties</param-value><!-- 配置文件 -->
</context-param>
<context-param>
<param-name>Owasp.CsrfGuard.Config.Print</param-name>
<param-value>true</param-value>
</context-param>
<!-- session监听器 --><!-- 基于复杂方案CsrfGuard的session监听器 -->
<listener>
<listener-class>org.owasp.csrfguard.CsrfGuardHttpSessionListener</listener-class>
</listener>
<listener>
<listener-class>org.owasp.csrfguard.CsrfGuardServletContextListener</listener-class>
</listener>
<filter>
<filter-name>CSRFGuard</filter-name>
<filter-class>org.owasp.csrfguard.CsrfGuardFilter</filter-class>
</filter>
<filter-mapping>
<filter-name>CSRFGuard</filter-name>
<url-pattern>/*</url-pattern>
</filter-mapping>
3)引入配置文件csrfguard.js csrfguard.properties(jar包META-INF里面有) csrfguard.properties配置文件中有几点需要注意:
可以指定加载的js,为方便管理,我放在WEB-INF目录下:
org.owasp.csrfguard.JavascriptServlet.sourceFile = WEB-INF/csrfguard.js
org.owasp.csrfguard.TokenName 对于nginx分发多servers的情况,nginx默认过滤带下划线的header,要么改掉nginx的配置,要么改这个参数的值。 参考:http://www.ttlsa.com/nginx/nginx-proxy_set_header
#>>>>>>>>>>>>>--author by caizhengluan e-mail: SvenAugustus@outlook.com
#Nginx ignores the underlined header variables by default.
# Please do not set "TokenName" has any underlines if you can't unkonwn how to change nginx's configuration.
org.owasp.csrfguard.TokenName=PAYCSRFTOKEN
#<<<<<<<<<<<<<--author by caizhengluan e-mail: SvenAugustus@outlook.com
org.owasp.csrfguard.JavascriptServlet.refererMatchDomain 对于nginx分发多servers的情况,需要设置为false
#>>>>>>>>>>>>>--author by caizhengluan e-mail: SvenAugustus@outlook.com
# If you have cluster and nginx, please set this value to false.Otherwise, you will can't visit into the servers when you access nginx address.
org.owasp.csrfguard.JavascriptServlet.refererMatchDomain = false
#<<<<<<<<<<<<<--author by caizhengluan e-mail: SvenAugustus@outlook.com
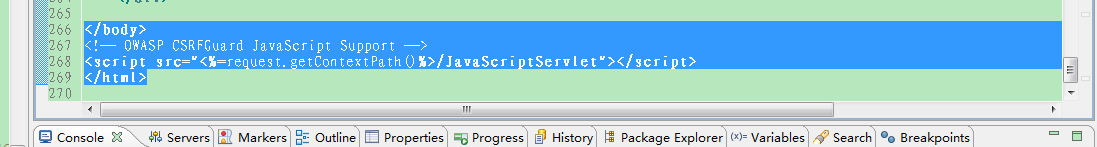
4、如何具体防御DWR和我们的页面? 在你的页面最后加上这么一句:
<!-- OWASP CSRFGuard JavaScript Support -->
<script src="<%=request.getContextPath()%>/JavaScriptServlet"></script>
转载自:https://my.oschina.net/langxSpirit/blog/678901






















 2035
2035

 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








