最近新上了一台PostgreSQL数据库服务器,研发提出了部分建议:
- 所有开发人员只能访问PostgreSQL数据库,不能远程ssh登录该数据库服务器
- DBA组的成员可以ssh访问PostgreSQL数据库服务器
- DBA的管理服务器可以ssh访问PostgreSQL服务器
- 补充:服务器所在网段可以不受限制的访问该PostgreSQL服务器
考虑使用防火墙来实现该安全访问需求。
- 启动防火墙前的检查操作
首先查看该服务器防火墙状态,并确定防火墙默认的zone。这里需要注意的是,千万不要查看防火墙是关闭状态后就第一时间启动防火墙,因为还不清楚防火墙的zone以及对应过滤规则,贸然启动可能会让服务器下线。
查看防火墙状态
# systemctl status firewalld● firewalld.service - firewalld - dynamic firewall daemon Loaded: loaded (/usr/lib/systemd/system/firewalld.service; disabled; vendor preset: enabled) Active: inactive (dead) Docs: man:firewalld(1)查看默认的zone
# cat /etc/firewalld/firewalld.conf......DefaultZone=public......查看默认的zone规则,这里可以看到默认的public zone已经包含允许ssh服务,这时,我们可以放心启动防火墙服务。这里需要注意的是:防火墙zone的配置文件读取顺序为/etc/firewalld/zones/*.xml--->/usr/lib/firewalld/zones/*.xml,如果/etc下的对应zone的位置文件不存在,则防火墙会读取/usr/lib下的对应zone的配置文件。
# cat /etc/firewalld/zones/public.xml<?xml version="1.0" encoding="utf-8"?>PublicFor use in public areas. You do not trust the other computers on networks to not harm your computer. Only selected incoming connections are accepted.启动防火墙
# systemctl enable firewalld# systemctl start firewalld# systemctl status firewalld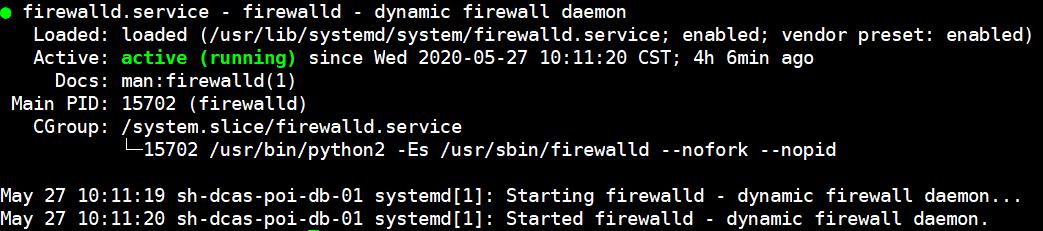
防火墙状态查看
- 配置准备使用的zone。
查看防火墙内置的zone有哪些
# firewall-cmd --get-zonesblock dmz drop external home internal public trusted work如果想以详细的方式显示每个zone的信息,可以使用如下命令
# firewall-cmd --list-all-zonesblock target: %%REJECT%% icmp-block-inversion: no interfaces: sources: services: ports: protocols: masquerade: no forward-ports: source-ports: icmp-blocks: rich rules: dmz target: default icmp-block-inversion: no interfaces: sources: services: ssh ports: protocols: masquerade: no forward-ports: source-ports: icmp-blocks: rich rules: drop target: DROP icmp-block-inversion: no interfaces: sources: services: ports: protocols: masquerade: no forward-ports: source-ports: icmp-blocks: rich rules: external target: default icmp-block-inversion: no interfaces: sources: services: ssh ports: protocols: masquerade: yes forward-ports: source-ports: icmp-blocks: rich rules: home target: default icmp-block-inversion: no interfaces: sources: services: dhcpv6-client mdns samba-client ssh ports: protocols: masquerade: no forward-ports: source-ports: icmp-blocks: rich rules: internal target: default icmp-block-inversion: no interfaces: sources: services: dhcpv6-client mdns samba-client ssh ports: protocols: masquerade: no forward-ports: source-ports: icmp-blocks: rich rules: public (active) target: default icmp-block-inversion: no interfaces: eth0 sources: services: dhcpv6-client ssh ports: protocols: masquerade: no forward-ports: source-ports: icmp-blocks: rich rules: trusted target: ACCEPT icmp-block-inversion: no interfaces: sources: services: ports: protocols: masquerade: no forward-ports: source-ports: icmp-blocks: rich rules: work target: default icmp-block-inversion: no interfaces: sources: services: dhcpv6-client ssh ports: protocols: masquerade: no forward-ports: source-ports: icmp-blocks: rich rules: 这里,我们选择使用“internal”zone作为我们配置防火墙的默认zone,查看该zone的详细信息,可以看到默认的zone“internal”已经包含部分规则,我们将这些规则清空,然后写入我们自己定义的规则
# firewall-cmd --zone="internal" --list-allinternal target: default icmp-block-inversion: no interfaces: sources: services: dhcpv6-client mdns samba-client ssh ports: protocols: masquerade: no forward-ports: source-ports: icmp-blocks: rich rules: 清空规则,这里需要注意的是--permanent参数指定从配置文件永久清除规则,如果不加--permanent条件,只是从当前载入内存的配置文件中清除规则,重启防火墙后还是会存在。
firewall-cmd --zone="internal" --permanent --remove-service=sshfirewall-cmd --zone="internal" --permanent --remove-service=mdnsfirewall-cmd --zone="internal" --permanent --remove-service=samba-clientfirewall-cmd --zone="internal" --permanent --remove-service=dhcpv6-clientfirewall-cmd --reload再次查看,说明内置的规则已经被我们清空
# firewall-cmd --zone="internal" --list-allinternal target: default icmp-block-inversion: no interfaces: sources: services: ports: protocols: masquerade: yes forward-ports: source-ports: icmp-blocks: rich rules: 下面我们写入自定义规则
firewall-cmd --zone="internal" --permanent --add-rich-rule="rule family="ipv4" source address="172.16.41.0/24" port protocol="tcp" port="22" accept"firewall-cmd --zone="internal" --permanent --add-rich-rule="rule family="ipv4" source address="10.188.104.168/32" port protocol="tcp" port="22" accept"firewall-cmd --zone="internal" --permanent --add-rich-rule="rule family="ipv4" source address="10.189.101.160/32" port protocol="tcp" port="22" accept"firewall-cmd --zone="internal" --permanent --add-rich-rule="rule family="ipv4" source address="0.0.0.0/0" port protocol="tcp" port="5432" accept"firewall-cmd --zone="internal" --permanent --add-rich-rule="rule family="ipv4" source address="10.0.0.0/8" accept"firewall-cmd --reload规则说明:
第一条规则允许172.16.41.0网段的IP地址访问PostgreSQL的22端口,即为ssh指定源IP,DBA组成员的网段
第二条和第三条规则指定具体的两台主机可以访问PostgreSQL服务器的22端口,该两台主机为DBA的管理服务器地址。
第四条允许任何源地址访问PostgreSQL服务器的5432端口。
第五条允许服务器网段10.0.0.0访问该PostgreSQL物理服务器。
规则添加完成后我们查看一下
# firewall-cmd --zone="internal" --list-allinternal (active) target: default icmp-block-inversion: no interfaces: eth0 sources: services: ports: protocols: masquerade: no forward-ports: source-ports: icmp-blocks: rich rules: rule family="ipv4" source address="172.16.41.0/24" port port="22" protocol="tcp" accept rule family="ipv4" source address="10.188.104.168/32" port port="22" protocol="tcp" acceptrule family="ipv4" source address="10.189.101.160/32" port port="22" protocol="tcp" acceptrule family="ipv4" source address="0.0.0.0/0" port port="5432" protocol="tcp" acceptrule family="ipv4" source address="10.0.0.0/8" accept- 将配置好的zone设置为默认的zone
查看当前默认的zone
# firewall-cmd --get-default-zonepublic设置默认的zone
# firewall-cmd --set-default-zone=internal此时防火墙就已经开始生效了。





















 1416
1416











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








