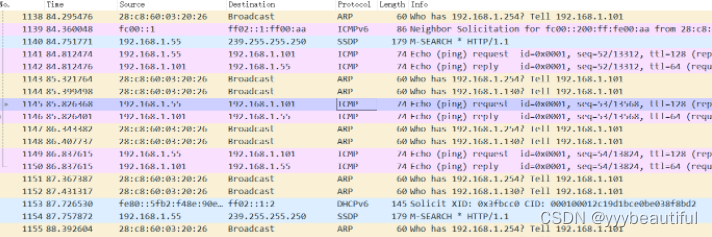
1-交换机端口镜像配置成功


- 可从一个端口获取其他流量进出情况,以便后续分析通信协议包
- 2号口为笔记本主机,可获取如台式机(3)和终端(4)通信信息,抓包如下
交换机192.168.1.100
笔记本(主站)192.168.1.127
融合终端 192.168.1.101
台式机 192.168.1.55
虚拟机 192.168.1.11
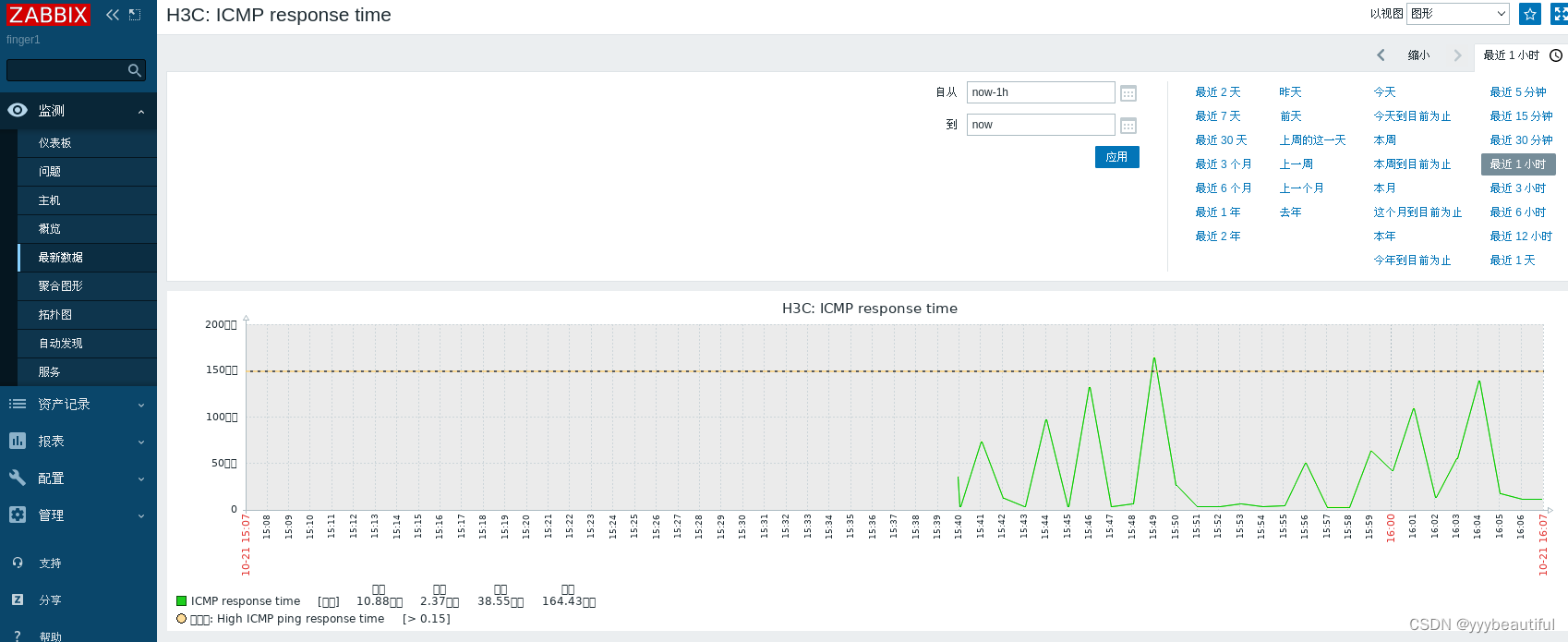
2-zabbix 通过SNMPv3 监控H3C交换机
- 登录交换机网址配置SNMP

- 配置团体、组、用户、trap

-
SNMP成功监测

-
其中的ICMP包监测如下

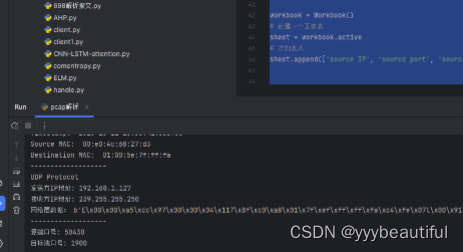
3-pcap文件解析
- 数据包解析
import dpkt
import socket
from datetime import datetime
from openpyxl import Workbook
workbook = Workbook()
sheet = workbook.active
sheet.append(['source IP', 'source port', 'source MAC','dst IP', 'dst port','dst MAC'])
def parse_packet(packet):
eth = dpkt.ethernet.Ethernet(packet)
src_mac = ':'.join('%02x' % b for b in eth.src)
print("Source MAC: ", src_mac)
dst_mac = ':'.join('%02x' % b for b in eth.dst)
print("Destination MAC: ", dst_mac)
print("-------------------")
# 解析IP数据报************************************************************
if isinstance(eth.data, dpkt.ip.IP):
ip = eth.data # 为IP数据报
protocol = ip.p
if protocol == dpkt.ip.IP_PROTO_TCP:
print("TCP Protocol")
elif protocol == dpkt.ip.IP_PROTO_UDP:
print("UDP Protocol")
elif protocol == dpkt.ip.IP_PROTO_ICMP:
print("ICMP Protocol")
else:
print("Unknown Protocol")
src_ip = socket.inet_ntoa(ip.src)
print("发送方IP地址:", src_ip)
dst_ip = socket.inet_ntoa(ip.dst)
print("接收方IP地址:", dst_ip)
print("网络层数据:", ip)
tcp = ip.data #tcp报文
print("-------------------")
# 解析传输层协议**********************************************************
if isinstance(tcp, dpkt.tcp.TCP):
src_port = tcp.sport
print("源端口号:", src_port)
dst_port = tcp.dport
print("目标端口号:", dst_port)
data = tcp.data
print("传输层数据为",data)
sheet.append([src_ip, src_port, src_mac, dst_ip, dst_port,dst_mac])
elif isinstance(ip.data, dpkt.udp.UDP):
udp = ip.data
src_port = udp.sport
print("源端口号:", src_port)
dst_port = udp.dport
print("目标端口号:", dst_port)
else:
pass
file = 'C:\\Users\\12446\\Desktop\\电力\\my\\1021.pcap'
with open(file, 'rb') as f:
pcap = dpkt.pcap.Reader(f)
for timestamp, buffer in pcap:
timestamp_dt = datetime.fromtimestamp(timestamp)
print("Timestamp: ", timestamp_dt)
parse_packet(buffer)
print("\n************************************\n")
workbook.save('network_traffic1.xlsx')
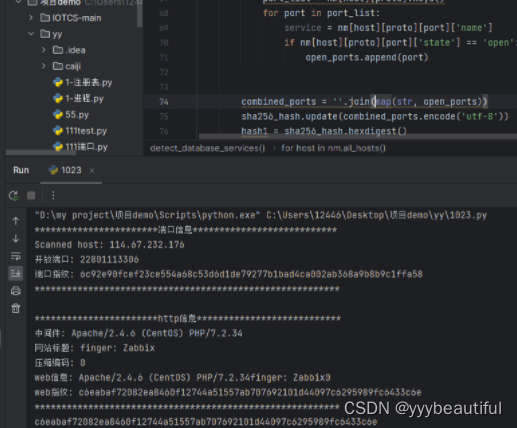
4-系统指纹
-
端口指纹+web指纹
-
端口指纹:基于namp
- 选用开放端口字符串,连接在一起使用sha256形成端口指纹hash
-
Web指纹是web服务组件在开发时留下的对其类型及版本进行标识的特殊信息,包括web服务器指纹、web运用指纹以及前端框架指纹等。
- web指纹选取:中间件+网站标题+压缩编码类型连接,其中压缩编码分为0(无)1(gzip)2(deflate)3(其他),使用sha256形成web指纹hash
-
两hash拼接一起使用sha256形成系统指纹hash
-
-
每60秒轮询一次
-
以自定义网站为例
指纹识别的几种方式
A、网页中发现关键字
B、特定文件的MD5(主要是静态文件、不一定要是MD5)
C、指定URL的关键字
D、指定URL的TAG模式
import time
import nmap
import hashlib
import requests
from bs4 import BeautifulSoup
sha256_hash = hashlib.sha256()
hash1=''
hash2=''
def detect_en(info):
# 将 Server Header 转换为小写,方便比较
info = info.lower()
if info=='gzip':
return '1'
elif info=='content-encoding header not found':
return '0'
elif info=='deflate':
return '2'
else:
return '3'
def get_website_info(url):
try:
response = requests.get(url)
# 获取响应头信息
server_info = response.headers.get('Server', 'Server header not found')
x_powered_by_info = response.headers.get('X-Powered-By', 'X-Powered-By header not found')
content_type = response.headers.get('Content-Type', 'Content-Type header not found')
content_encoding = response.headers.get('Content-Encoding', 'Content-Encoding header not found')
cache_control = response.headers.get('Cache-Control', 'Cache-Control header not found')
content_length = response.headers.get('Content-Length', 'Content-Length header not found')
last_modified = response.headers.get('Last-Modified', 'Last-Modified header not found')
etag = response.headers.get('ETag', 'ETag header not found')
status_code = response.status_code
print("中间件:", server_info)
soup = BeautifulSoup(response.content, 'html.parser')
title = soup.title.string if soup.title else 'Title not found'
print("网站标题:", title)
detected_encode = detect_en(content_encoding)
print("压缩编码:", detected_encode)
# http消息连接 中间件+网站标题+压缩编码类型
infor = server_info+title+detected_encode
print("web信息:",infor)
sha256_hash.update(infor.encode('utf-8'))
hash2 = sha256_hash.hexdigest()
print(f"web指纹: {hash2}")
except requests.exceptions.RequestException as e:
print("An error occurred:", str(e))
def detect_database_services(host):
nm = nmap.PortScanner()
nm.scan(hosts=host, arguments='-F') # Fast scan to check common ports
for host in nm.all_hosts():
print(f"Scanned host: {host}")
open_ports = []
for proto in nm[host].all_protocols():
port_list = nm[host][proto].keys()
for port in port_list:
service = nm[host][proto][port]['name']
if nm[host][proto][port]['state'] == 'open':
open_ports.append(port)
combined_ports = ''.join(map(str, open_ports))
sha256_hash.update(combined_ports.encode('utf-8'))
hash1 = sha256_hash.hexdigest()
print(f"开放端口: {combined_ports}")
print(f"端口指纹: {hash1}")
if __name__ == "__main__":
while True:
print("***********************端口信息***************************")
target_host = "114.67.232.176" # 服务器主机名或IP地址
detect_database_services(target_host)
print("*********************************************************\n")
print("***********************http信息***************************")
url = "http://114.67.232.176/zabbix"
#url = "http://www.baidu.com"
get_website_info(url)
print("*********************************************************")
sha256_hash.update((hash1+hash2).encode('utf-8'))
hash = sha256_hash.hexdigest()
print(hash)
time.sleep(60)





















 853
853











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








