1. 网络拓扑
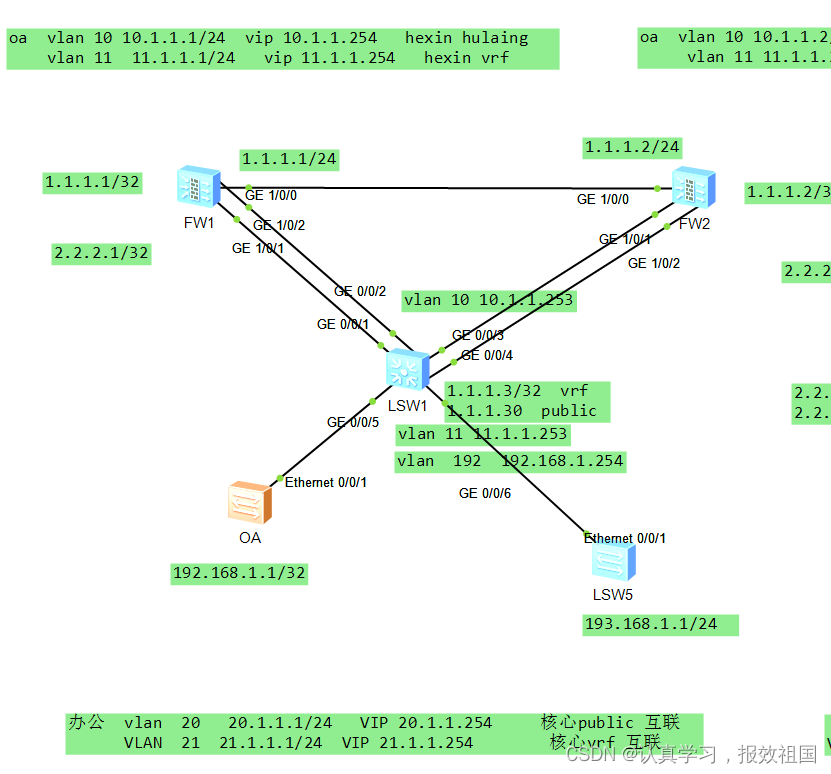
2、 拓扑解释
1 有两种业务oa 和办公
2 oa vlan10 vlan11 vlan10 和核心交换机poublic 互联
vlan11 和核心交换机vrf oa 互联
3 办公 vlan 20 vlan21 vlan20 和核心交换机public 互联
vlan21 和核心交换机vrf bangong 互联
4 核心上为了区分不同的业务oa 和办公 vlan 192 vlan 11 用vrf oa 绑定
办公 vlan193 和vlan21 用 vrf bangong 绑定
5 所有的路由在核心public 汇总
3 、 路由转发过程
1 由于在核心交换机上用vpn 区分了不同的业务,那么在防火墙也需要用不同的虚拟墙与之对应
2 oa----核心oa-vrf ---------------vlan11 vrf-----------------fw1oavlan 11------fw1 oavlan10 vrf-------核心vlan10
3也就是说核心交换机实际上用了两种不同的路由一种是vrf 路由一种是普通路由,vrf 路由就是为了区分不同的业务,能够让路由走不同的虚拟防火墙, 最后再通过public 公共路由汇总
4 所以在核心交换上如果用不同的ospf 那么一定要保证vrf 的routerid 和普通路由的id 不一致
5 因为有两种业务,一种业务用ospf10 一种业务用ospf20 为了区分,但是核心交换机上的public ospf1 是唯一的,所以相当于在全网保证router id 的唯一性,否则出问题
6 策略放行,在各自的虚拟防火墙上放行业务
4、 逻辑拓扑介绍
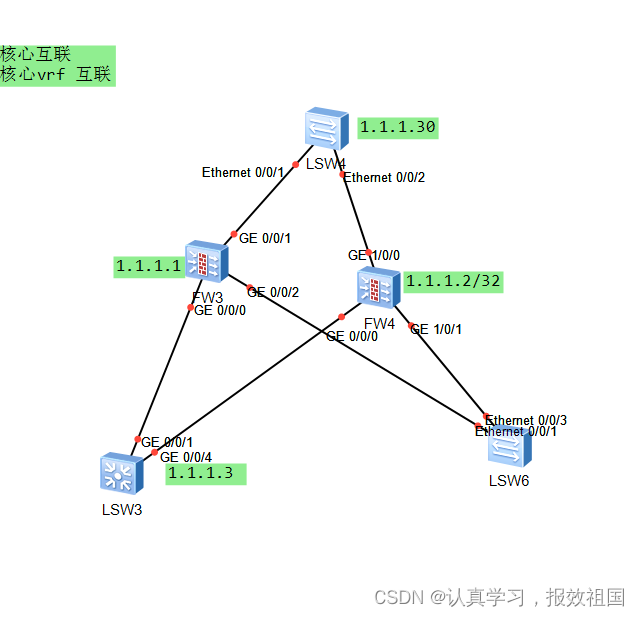
lsw3--fw3 走的是vrf -----lsw4 走的是public
lsw3-fw4-走的是vrf--lsw4走的是public 这里需要说明相当于把核心交换机分成了lsw3 和lsw4 一个走的是vrf 一个走的是public ,为了保证路由的正确性,一定routerid 唯一!!!
同理针对不同的业务用不同的进程区分,但是最后都是在public 汇总,那么不同进程的routerid 也要唯一 这个很关键
5 关键配置
核心上
<hexin>system-view
Enter system view, return user view with Ctrl+Z.
[hexin]
[hexin]dis
[hexin]display cu
[hexin]display current-configuration
#
sysname hexin
#
vlan batch 10 to 11 20 to 21 192 to 193
#
cluster enable
ntdp enable
ndp enable
#
drop illegal-mac alarm
#
diffserv domain default
#
ip vpn-instance bangong
ipv4-family
route-distinguisher 192:2
vpn-target 192:2 export-extcommunity
vpn-target 192:2 import-extcommunity
#
ip vpn-instance oa
ipv4-family
route-distinguisher 192:1
vpn-target 192:1 export-extcommunity
vpn-target 192:1 import-extcommunity
#
drop-profile default
#
aaa
authentication-scheme default
authorization-scheme default
accounting-scheme default
domain default
domain default_admin
local-user admin password simple admin
local-user admin service-type http
#
interface Vlanif1
#
interface Vlanif10
ip address 10.1.1.253 255.255.255.0
#
interface Vlanif11
ip binding vpn-instance oa
ip address 11.1.1.253 255.255.255.0
#
interface Vlanif20
ip address 20.1.1.253 255.255.255.0
#
interface Vlanif21
ip binding vpn-instance bangong
ip address 21.1.1.253 255.255.255.0
#
interface Vlanif192
ip binding vpn-instance oa
ip address 192.168.1.254 255.255.255.0
#
interface Vlanif193
ip binding vpn-instance bangong
ip address 193.168.1.254 255.255.255.0
#
interface MEth0/0/1
#
interface Eth-Trunk1
port link-type trunk
undo port trunk allow-pass vlan 1
port trunk allow-pass vlan 2 to 4094
#
interface Eth-Trunk2
port link-type trunk
undo port trunk allow-pass vlan 1
port trunk allow-pass vlan 2 to 4094
#
interface GigabitEthernet0/0/1
eth-trunk 1
#
interface GigabitEthernet0/0/2
eth-trunk 1
#
interface GigabitEthernet0/0/3
eth-trunk 2
#
interface GigabitEthernet0/0/4
eth-trunk 2
#
interface GigabitEthernet0/0/5
port link-type access
port default vlan 192
#
interface GigabitEthernet0/0/6
port link-type access
port default vlan 193
#
interface GigabitEthernet0/0/7
#
interface GigabitEthernet0/0/8
#
interface GigabitEthernet0/0/9
#
interface GigabitEthernet0/0/10
#
interface GigabitEthernet0/0/11
#
interface GigabitEthernet0/0/12
#
interface GigabitEthernet0/0/13
#
interface GigabitEthernet0/0/14
#
interface GigabitEthernet0/0/15
#
interface GigabitEthernet0/0/16
#
interface GigabitEthernet0/0/17
#
interface GigabitEthernet0/0/18
#
interface GigabitEthernet0/0/19
#
interface GigabitEthernet0/0/20
#
interface GigabitEthernet0/0/21
#
interface GigabitEthernet0/0/22
#
interface GigabitEthernet0/0/23
#
interface GigabitEthernet0/0/24
#
interface NULL0
#
ospf 1 router-id 1.1.1.30
area 0.0.0.0
network 10.1.1.0 0.0.0.255
network 20.1.1.0 0.0.0.255
#
ospf 10 router-id 1.1.1.3 vpn-instance oa
silent-interface Vlanif192
area 0.0.0.0
network 11.1.1.0 0.0.0.255
network 192.168.1.0 0.0.0.255
#
ospf 20 router-id 2.2.2.3 vpn-instance bangong
silent-interface Vlanif193
area 0.0.0.0
network 21.1.1.0 0.0.0.255
network 193.168.1.0 0.0.0.255
#
user-interface con 0
user-interface vty 0 4
#
===========================
虚拟墙oa l2tp domain suffix-separator @
#
firewall defend action discard
#
page-setting
password-policy
level high
#
time-range worktime
period-range 08:00:00 to 18:00:00 working-day
#
aaa
authentication-scheme default
authentication-scheme admin_local
authentication-scheme admin_radius_local
authentication-scheme admin_hwtacacs_local
authentication-scheme admin_ad_local
authentication-scheme admin_ldap_local
authentication-scheme admin_radius
authentication-scheme admin_hwtacacs
authentication-scheme admin_ad
authorization-scheme default
accounting-scheme default
domain default
service-type internetaccess ssl-vpn l2tp ike
internet-access mode password
reference user current-domain
role system-admin
role device-admin
role device-admin(monitor)
role audit-admin
#
l2tp-group default-lns
#
interface Virtual-if3
#
sa
#
firewall zone local
set priority 100
#
firewall zone trust
set priority 85
#
firewall zone untrust
set priority 5
#
firewall zone dmz
set priority 50
#
location
#
multi-linkif
mode proportion-of-weight
#
security-policy
#
auth-policy
#
traffic-policy
#
policy-based-route
#
nat-policy
#
quota-policy
#
pcp-policy
#
return
HRP_M<fw1>
HRP_M<fw1>sy
HRP_M<fw1>system-view
Enter system view, return user view with Ctrl+Z.
HRP_M[fw1]sw
HRP_M[fw1]switch vs
HRP_M[fw1]switch vsys oa
HRP_M<fw1-oa>dis cu
HRP_M<fw1-oa>dis current-configuration
2023-04-02 03:02:21.500
#
switch vsys oa
#
l2tp domain suffix-separator @
#
firewall defend action discard
#
page-setting
password-policy
level high
#
time-range worktime
period-range 08:00:00 to 18:00:00 working-day
#
aaa
authentication-scheme default
authentication-scheme admin_local
authentication-scheme admin_radius_local
authentication-scheme admin_hwtacacs_local
authentication-scheme admin_ad_local
authentication-scheme admin_ldap_local
authentication-scheme admin_radius
authentication-scheme admin_hwtacacs
authentication-scheme admin_ad
authorization-scheme default
accounting-scheme default
domain default
service-type internetaccess ssl-vpn l2tp ike
internet-access mode password
reference user current-domain
role system-admin
role device-admin
role device-admin(monitor)
role audit-admin
#
interface Vlanif10
ip binding vpn-instance oa
ip address 10.1.1.1 255.255.255.0
vrrp vrid 1 virtual-ip 10.1.1.254 active
ospf dr-priority 0
service-manage http permit
service-manage https permit
service-manage ping permit
service-manage ssh permit
service-manage telnet permit
#
interface Vlanif11
ip binding vpn-instance oa
ip address 11.1.1.1 255.255.255.0
vrrp vrid 2 virtual-ip 11.1.1.254 active
ospf dr-priority 0
service-manage http permit
service-manage https permit
service-manage ping permit
service-manage ssh permit
service-manage telnet permit
#
l2tp-group default-lns
#
interface Virtual-if1
#
sa
#
firewall zone local
set priority 100
#
firewall zone trust
set priority 85
add interface Vlanif10
#
firewall zone untrust
set priority 5
add interface Vlanif11
#
firewall zone dmz
set priority 50
#
location
#
multi-linkif
mode proportion-of-weight
#
security-policy
rule name zhilian
source-zone local
source-zone trust
source-zone untrust
destination-zone local
destination-zone trust
destination-zone untrust
source-address 10.1.1.0 mask 255.255.255.0
source-address 11.1.1.0 mask 255.255.255.0
destination-address 10.1.1.0 mask 255.255.255.0
destination-address 11.1.1.0 mask 255.255.255.0
action permit
rule name tong
source-zone trust
source-zone untrust
destination-zone trust
destination-zone untrust
source-address 192.168.1.0 mask 255.255.255.0
source-address 193.168.1.0 mask 255.255.255.0
destination-address 192.168.1.0 mask 255.255.255.0
destination-address 193.168.1.0 mask 255.255.255.0
action permit
#
auth-policy
#
traffic-policy
#
policy-based-route
#
nat-policy
#
quota-policy
#
pcp-policy
#
return
虚拟墙办公
service-manage https permit
service-manage ping permit
service-manage ssh permit
service-manage telnet permit
#
l2tp-group default-lns
#
interface Virtual-if1
#
sa
#
firewall zone local
set priority 100
#
firewall zone trust
set priority 85
add interface Vlanif10
#
firewall zone untrust
set priority 5
add interface Vlanif11
#
firewall zone dmz
set priority 50
#
location
#
multi-linkif
mode proportion-of-weight
#
security-policy
rule name zhilian
source-zone local
source-zone trust
source-zone untrust
destination-zone local
destination-zone trust
destination-zone untrust
source-address 10.1.1.0 mask 255.255.255.0
source-address 11.1.1.0 mask 255.255.255.0
destination-address 10.1.1.0 mask 255.255.255.0
destination-address 11.1.1.0 mask 255.255.255.0
action permit
rule name tong
source-zone trust
source-zone untrust
destination-zone trust
destination-zone untrust
source-address 192.168.1.0 mask 255.255.255.0
source-address 193.168.1.0 mask 255.255.255.0
destination-address 192.168.1.0 mask 255.255.255.0
destination-address 193.168.1.0 mask 255.255.255.0
action permit
#
auth-policy
#
traffic-policy
#
policy-based-route
#
nat-policy
#
quota-policy
#
pcp-policy
#
return
HRP_M<fw1-oa>
HRP_M<fw1-oa>quit
HRP_M[fw1]
HRP_M[fw1]
HRP_M[fw1]sw
HRP_M[fw1]switch vd
HRP_M[fw1]switch vs
HRP_M[fw1]switch vsys ba
HRP_M[fw1]switch vsys bangong
HRP_M<fw1-bangong>
HRP_M<fw1-bangong>dis cu
HRP_M<fw1-bangong>dis current-configuration
2023-04-02 03:03:14.760
#
switch vsys bangong
#
l2tp domain suffix-separator @
#
firewall defend action discard
#
page-setting
password-policy
level high
#
time-range worktime
period-range 08:00:00 to 18:00:00 working-day
#
aaa
authentication-scheme default
authentication-scheme admin_local
authentication-scheme admin_radius_local
authentication-scheme admin_hwtacacs_local
authentication-scheme admin_ad_local
authentication-scheme admin_ldap_local
authentication-scheme admin_radius
authentication-scheme admin_hwtacacs
authentication-scheme admin_ad
authorization-scheme default
accounting-scheme default
domain default
service-type internetaccess ssl-vpn l2tp ike
internet-access mode password
reference user current-domain
role system-admin
role device-admin
role device-admin(monitor)
role audit-admin
#
interface Vlanif20
ip binding vpn-instance bangong
ip address 20.1.1.1 255.255.255.0
vrrp vrid 3 virtual-ip 20.1.1.254 active
ospf dr-priority 0
service-manage http permit
service-manage https permit
service-manage ping permit
service-manage ssh permit
service-manage telnet permit
#
interface Vlanif21
ip binding vpn-instance bangong
ip address 21.1.1.1 255.255.255.0
vrrp vrid 5 virtual-ip 21.1.1.254 active
ospf dr-priority 0
service-manage http permit
service-manage https permit
service-manage ping permit
service-manage ssh permit
service-manage telnet permit
#
l2tp-group default-lns
#
interface Virtual-if2
#
sa
#
firewall zone local
set priority 100
#
firewall zone trust
set priority 85
add interface Vlanif20
#
firewall zone untrust
set priority 5
add interface Vlanif21
#
firewall zone dmz
set priority 50
#
location
#
multi-linkif
mode proportion-of-weight
#
security-policy
rule name zhilian
source-zone local
source-zone trust
source-zone untrust
destination-zone local
destination-zone trust
destination-zone untrust
source-address 20.1.1.0 mask 255.255.255.0
source-address 21.1.1.0 mask 255.255.255.0
destination-address 20.1.1.0 mask 255.255.255.0
destination-address 21.1.1.0 mask 255.255.255.0
action permit
rule name tong
source-zone trust
source-zone untrust
destination-zone trust
destination-zone untrust
source-address 192.168.1.0 mask 255.255.255.0
source-address 193.168.1.0 mask 255.255.255.0
destination-address 192.168.1.0 mask 255.255.255.0
destination-address 193.168.1.0 mask 255.255.255.0
action permit
#
auth-policy
#
traffic-policy
#
policy-based-route
#
nat-policy
#
quota-policy
#
pcp-policy
#
return
==================
root
hrp enable
hrp interface GigabitEthernet1/0/0 remote 1.1.1.2
hrp timer hello 500
hrp standby config enable
hrp preempt delay 5
hrp track interface GigabitEthernet1/0/1
hrp track interface GigabitEthernet1/0/2
vsys enable
resource-class r0
resource-class 1
#
#
vsys name oa 1
assign resource-class 1
assign vlan 10
assign vlan 11
#
vsys name bangong 2
assign resource-class 1
assign vlan 20
assign vlan 21
#
interface Vlanif10
ip binding vpn-instance oa
ip address 10.1.1.1 255.255.255.0
vrrp vrid 1 virtual-ip 10.1.1.254 active
ospf dr-priority 0
service-manage http permit
service-manage https permit
service-manage ping permit
service-manage ssh permit
service-manage telnet permit
#
interface Vlanif11
ip binding vpn-instance oa
ip address 11.1.1.1 255.255.255.0
vrrp vrid 2 virtual-ip 11.1.1.254 active
ospf dr-priority 0
service-manage http permit
service-manage https permit
service-manage ping permit
service-manage ssh permit
service-manage telnet permit
#
interface Vlanif20
ip binding vpn-instance bangong
ip address 20.1.1.1 255.255.255.0
vrrp vrid 3 virtual-ip 20.1.1.254 active
ospf dr-priority 0
service-manage http permit
service-manage https permit
service-manage ping permit
service-manage ssh permit
service-manage telnet permit
#
interface Vlanif21
ip binding vpn-instance bangong
ip address 21.1.1.1 255.255.255.0
vrrp vrid 5 virtual-ip 21.1.1.254 active
ospf dr-priority 0
service-manage http permit
service-manage https permit
service-manage ping permit
service-manage ssh permit
service-manage telnet permit
#
ospf 10 router-id 1.1.1.1 vpn-instance oa
area 0.0.0.0
network 10.1.1.0 0.0.0.255
network 11.1.1.0 0.0.0.255
#
ospf 20 router-id 2.2.2.1 vpn-instance bangong
area 0.0.0.0
network 20.1.1.0 0.0.0.255
network 21.1.1.0 0.0.0.255
=====================================





















 937
937











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








