DNUICTF反思总结
自己还是太菜了。。。
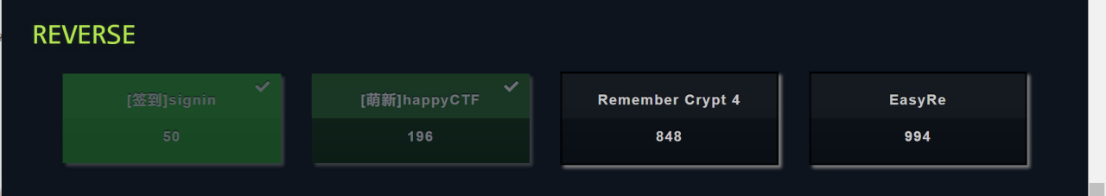
1.signin 明码
2 happyctf
异或20
#include <iostream>
using namespace std;
int main(){
int a[24]={114,120,117,115,111,67,113,120,119,123,121,
113,75,96,123,75,90,113,97,103,123,114,96,105};
for(int i=0;i<24;i++)
a[i]^=20;
for(int i=0;i<24;i++){
char p=a[i];
cout<<p;
}
}
3 Remember Crypt 4
我太菜了,没学过rc4。赛后狠狠的看了看算法代码。来自百度百科
先初始化
void rc4_init(unsigned int*s, unsigned char*key, unsigned long Len)
{
int i = 0, j = 0;
char k[256] = { 0 };
unsigned char tmp = 0;
for (i = 0; i<256; i++)
{
s[i] = i;
k[i] = key[i%Len];
}
for (i = 0; i<256; i++)
{
j = (j + s[i] + k[i]) % 256;
tmp = s[i];
s[i] = s[j];
s[j] = tmp;
}
}
建立一个s的256个成员的数组。内容为从0到255,且根据密钥被完全打乱。
void rc4_crypt(unsigned int*s, unsigned char*Data, unsigned long Len)
{
int i = 0, j = 0, t = 0;
unsigned long k = 0;
unsigned char tmp;
for (k = 0; k<Len; k++)
{
i = (i + 1) % 256;
j = (j + s[i]) % 256;
tmp = s[i];
s[i] = s[j];//交换s[x]和s[y]
s[j] = tmp;
t = (s[i] + s[j]) % 256;
Data[k] ^= s[t];
}
}
再打乱一下s,然后进行异或操作。
这是对称加密,加密函数即为解密函数。
init对应sub_140001120()
crypt对应sub_140001240()
最后异或34再进行比较
key=“12345678abcdefghijklmnopqrspxyz”
#include<stdio.h>
#include<string.h>
#include <iostream>
using namespace std;
typedef unsigned longULONG;
void rc4_init(unsigned int*s, unsigned char*key, unsigned long Len)
{
int i = 0, j = 0;
char k[256] = { 0 };
unsigned char tmp = 0;
for (i = 0; i<256; i++)
{
s[i] = i;
k[i] = key[i%Len];
}
for (i = 0; i<256; i++)
{
j = (j + s[i] + k[i]) % 256;
tmp = s[i];
s[i] = s[j];
s[j] = tmp;
}
}
void rc4_crypt(unsigned int*s, unsigned char*Data, unsigned long Len)
{
int i = 0, j = 0, t = 0;
unsigned long k = 0;
unsigned char tmp;
for (k = 0; k<Len; k++)
{
i = (i + 1) % 256;
j = (j + s[i]) % 256;
tmp = s[i];
s[i] = s[j];//交换s[x]和s[y]
s[j] = tmp;
t = (s[i] + s[j]) % 256;
Data[k] ^= s[t];
}
}
int main()
{
unsigned int s[256] = { 0 }, s2[256] = { 0 };//S-box
char key[256] = { "12345678abcdefghijklmnopqrspxyz" };
char pData[512] = {0x9E,0xE7,0x30,0x5F,0xA7,0x01,0xA6,0x53,0x59,0x1B,0x0A,0x20,0xF1,0x73,0xD1,0x0E,0xAB,0x09,0x84,0x0E,0x8D, 0x2B};
unsigned long len = strlen(pData);
for(int i=0;i<22;i++)
pData[i]^=0x22;
rc4_init(s, (unsigned char*)key, strlen(key));
for (i = 0; i<256; i++)
{
cout<<s[i]<<" ";
if (i && (i + 1) % 16 == 0)putchar('\n');
}
printf("\n\n");
for (i = 0; i<256; i++)
{
s2[i] = s[i];
}
rc4_crypt(s2, (unsigned char*)pData, len);
printf("pData=%s\n\n", pData);
return 0;
}
4 easyre
一点都不easy,我没学过linux系统vm信号转换。就看一个个信号函数蒙圈。(做题时:s1?s1是什么?在哪里赋的值?为什么有个区域一直被修改?)看别人题解后:原来如此。虽然还是不会做。
开始读取4019c0的指令
看别人writeup的解析https://mp.weixin.qq.com/s/KgxHOFH52EE8z7NnMTSIDA
解码出来是汇编指令
赋值是push pop 进行的。其中 call 29是异或,call 64是加。

最后再与s2比较,相等就行了。























 1582
1582











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?










