[广东省大学生攻防大赛 2022]pyre
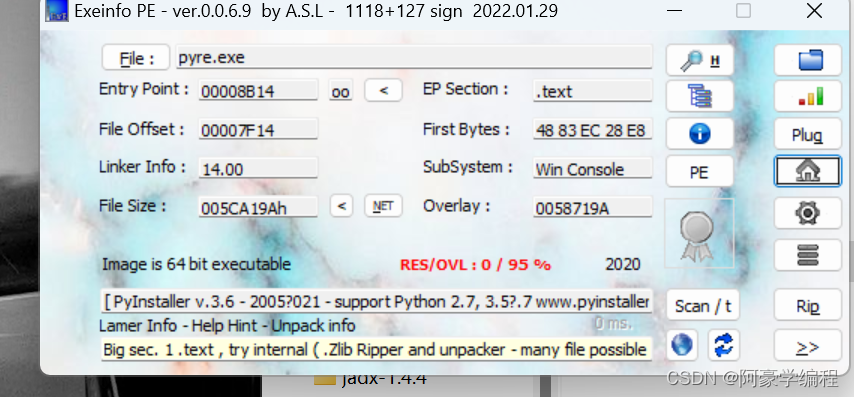
下载附件进行查壳得知为64位文件。
用ida打开 SHIFT+12
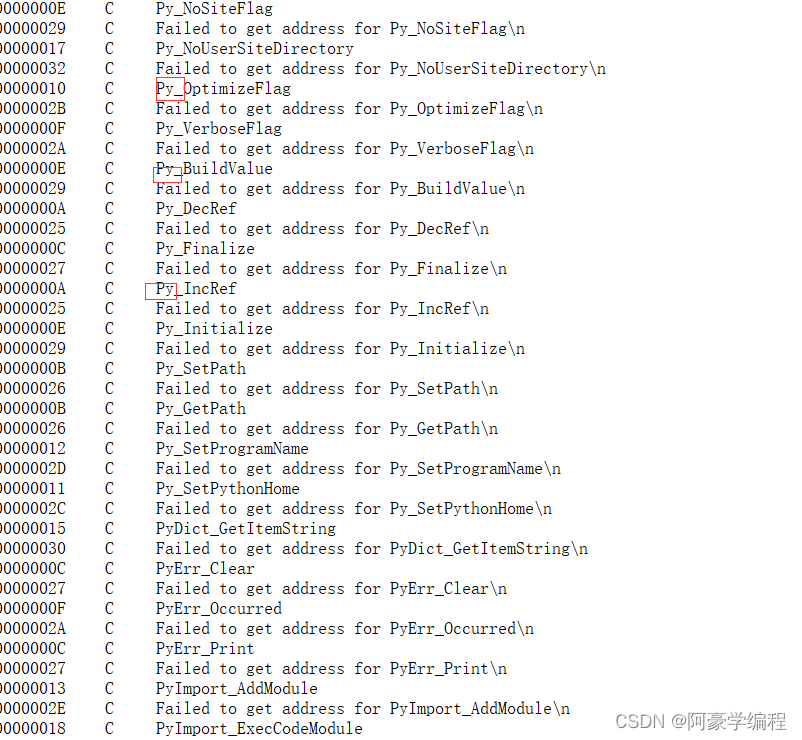
看到多为py 可以断定为python反编译文件
然后使用一些python反编译工具提取pyc文件
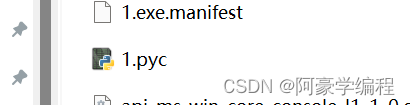
然后在网上随便搜索一个在线反编译就能得到python源码
def check():
a = input('plz input your flag:')
c = [
144,
163,
158,
177,
121,
39,
58,
58,
91,
111,
25,
158,
72,
53,
152,
78,
171,
12,
53,
105,
45,
12,
12,
53,
12,
171,
111,
91,
53,
152,
105,
45,
152,
144,
39,
171,
45,
91,
78,
45,
158,
8]
if len(a) != 42:
print('wrong length')
return 0
b = None
for i in range(len(a)):
if ord(a[i]) * 33 % b != c[i]:
print('wrong')
return None
print('win')
check()
拿到源码时,看到逻辑很简单,就是明文进行*33后在对b求模,
问题是b不知道,这是可以根据常识经验进行爆破得出b
int main() {
char a[4] = "flag";
int c[4] = { 144,163,158,177 };
for (int i = 0; i < 4; i++) {
for (int b = 127; b < 1000; b++) {
if (((int)a[i]) * 33 % b == c[i]) {
printf("%d ", b);
break;
}
}
}
return 0;
}得出b=179
然后在进行爆破求得flag
int main() {
//b=179
int a[42] = { 144,
163,
158,
177,
121,
39,
58,
58,
91,
111,
25,
158,
72,
53,
152,
78,
171,
12,
53,
105,
45,
12,
12,
53,
12,
171,
111,
91,
53,
152,
105,
45,
152,
144,
39,
171,
45,
91,
78,
45,
158,
8 };
int b = 179;
// b[i]%179=c[i]
for(int i=0;i<42;i++){
for (int j = 32; j < 127; j++) {
if (j * 33 % b == a[i]) {
printf("%c", j);
break;
}
}
}
return 0;
}//flag{2889e7a3-0d6b-4cbb-b6e9-04c0f26c9dca}[HGAME 2023 week1]encode
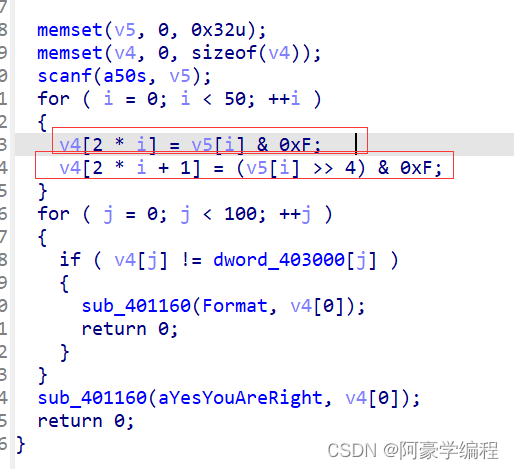
主要步骤
爆破求解
int main() {
int a[] = {
8,
6,
7,
6,
1,
6,
13,
6,
5,
6,
11,
7,
5,
6,
14,
6,
3,
6,
15,
6,
4,
6,
5,
6,
15,
5,
9,
6,
3,
7,
15,
5,
5,
6,
1,
6,
3,
7,
9,
7,
15,
5,
6,
6,
15,
6,
2,
7,
15,
5,
1,
6,
15,
5,
2,
7,
5,
6,
6,
7,
5,
6,
2,
7,
3,
7,
5,
6,
15,
5,
5,
6,
14,
6,
7,
6,
9,
6,
14,
6,
5,
6,
5,
6,
2,
7,
13,
7,
0,
0,
0,
0,
0,
0,
0,
0,
0,
0,
0,
0
};
for (int i = 0; i < 100; ++i) {
for (int j = 32; j < 127; j++) { //爆破
if (a[2 * i] == (j & 0xF) && a[2 * i + 1] == ((j >> 4) & 0xF)) {
printf("%c", j);
}
}
}
return 0;
}//hgame{encode_is_easy_for_a_reverse_engineer}
[WUSTCTF 2020]level3
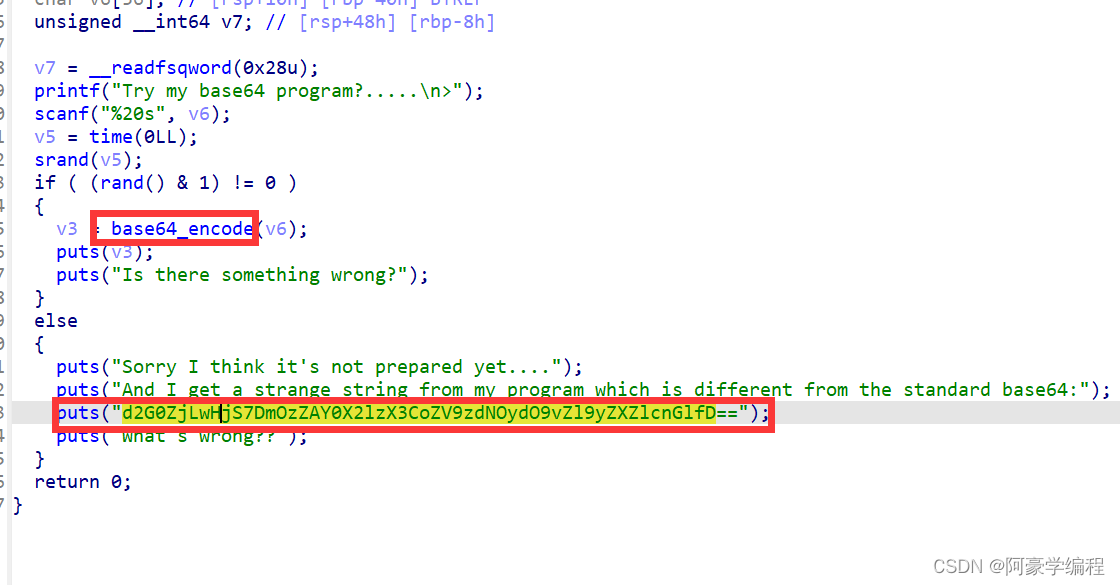
主要程序逻辑清晰可见,经过base64编码得到下边一串字符串。但直接解密发现又不是想要得结果。有猫腻。观察其他函数发现: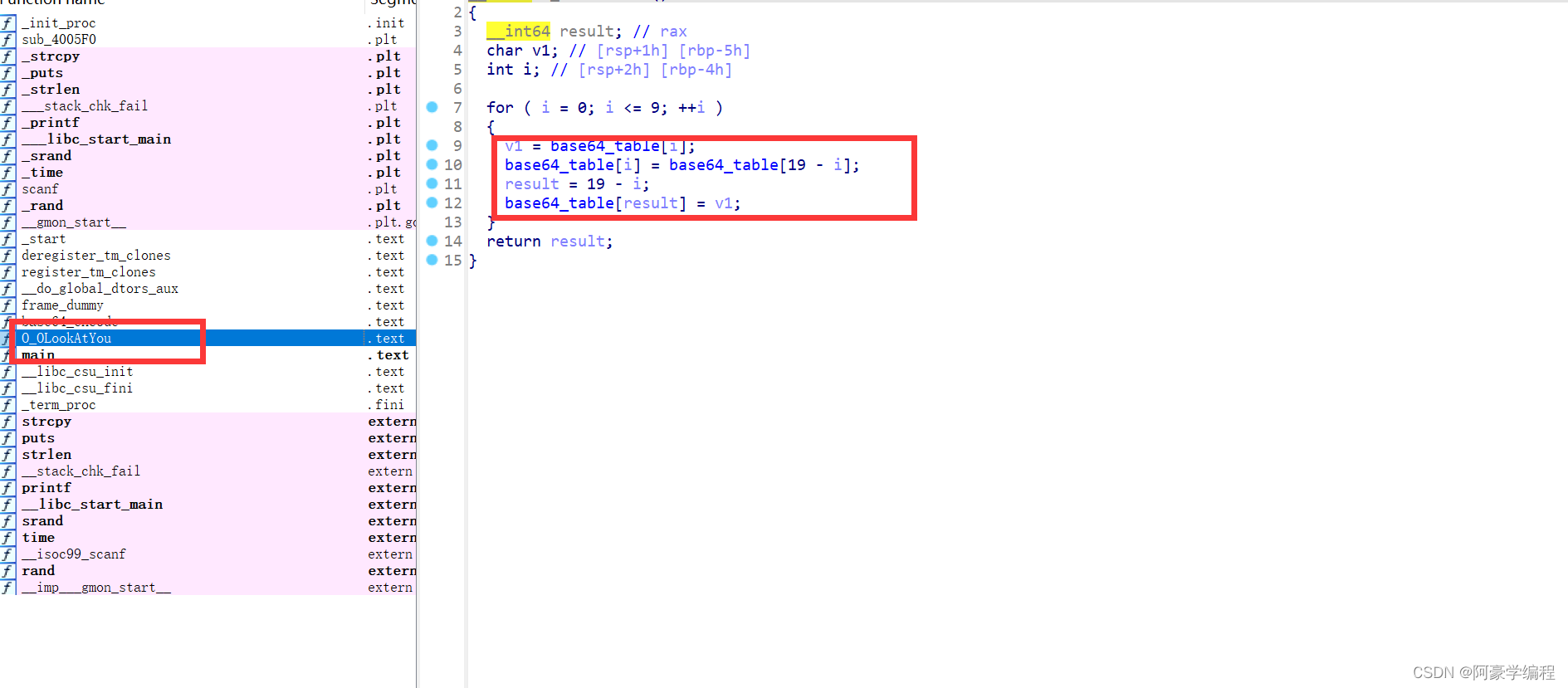
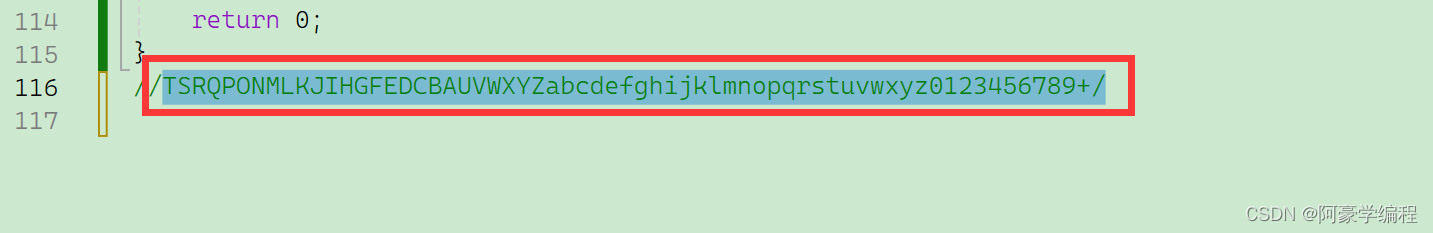
看到就是将其中某10位与另外十位进行交换位置。进行逻辑分析得到魔改得base64:
 找一个在线网站,即可解密
找一个在线网站,即可解密






















 902
902











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








