nmap绕过防火墙扫描参数
Hey hackers!!!
嘿,黑客!!!
We have already discussed about basic commands on Nmap and also the cheat sheet for Nmap, which i believe helped you for performing scans on networks , today we are going to discuss about some more Nmap commands ,such as Stealth scan , OS detection , Zombie scan, Bypassing Firewall Commands and many more.
我们已经讨论过Nmap上的基本命令以及Nmap的备忘单,我相信它可以帮助您在网络上执行扫描,今天我们将讨论更多Nmap命令,例如隐形扫描,操作系统检测,僵尸扫描,绕过防火墙命令等等。
TCP连接扫描 (TCP Connect Scan)
First scan we will look is TCP scan , this scan is often considered the most basic and stable of all the port scans because it actually completes the three way handshake and then tears down the connection gracefully.
我们将看的第一个扫描是TCP扫描,该扫描通常被认为是所有端口扫描中最基本,最稳定的扫描,因为它实际上完成了三向握手 ,然后正常地断开了连接。
nmap -sT 192.168.1.3However, we have discussed this command prior , but for better understanding i have also made use of Wireshark to record the behavior of the packets.
但是,我们之前已经讨论了此命令,但是为了更好地理解,我还使用Wireshark记录了数据包的行为。
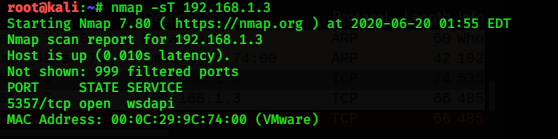
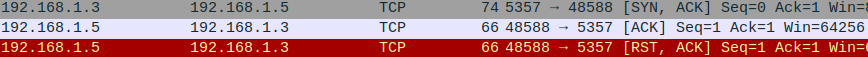
You can see from above wireshark output that it actually completed Three Way handshake.
您可以从wireshark输出的上方看到它实际上完成了“三向”握手。
TCP SYN扫描 (TCP SYN Scan)
The SYN scan is arguably the most popular Nmap port scan.As is the the default Nmap scanning technique i.e even if you don’t specify the “-s” switch, Nmap will use the SYN scan by default.
SYN扫描可以说是最受欢迎的Nmap端口扫描。这是默认的Nmap扫描技术,即,即使您未指定“ -s”开关,Nmap也会默认使用SYN扫描。
SYN scan is faster than TCP scan .
SYN扫描比TCP扫描更快。
nmap -sS 192.168.1.3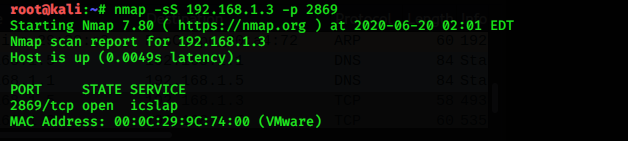
As you can se that i have also made use of “-p” switch which allows you to scan a specific port.(2869 in this case , which is intentionally left open).
如您所知,我还使用了“ -p”开关,该开关可让您扫描特定端口。(在本例中为2869,有意将其保持打开状态)。
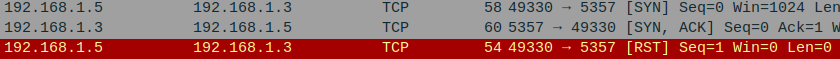
Below is the wireshark output for the same.
下面是相同的wireshark输出。








 最低0.47元/天 解锁文章
最低0.47元/天 解锁文章














 2040
2040











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








